Cybersecurity Decision Makers: Who They Are, What They Want, and How to Reach Them
Cybercrime costs the global economy an estimated $10.5 trillion per year, and the number keeps climbing. The average data breach runs $4.63M. The people responsible for preventing those losses - CISOs, security VPs, IT directors - now oversee everything from AI governance to OT/ICS security to board-level regulatory compliance. The cybersecurity decision maker role has expanded so far beyond its original scope that most vendors selling into this space are targeting the wrong person, with the wrong message, at the wrong time.
That gap between who vendors think makes security purchases and who actually does is where pipeline goes to die.
Who Makes Cybersecurity Purchases?
Most content about security buying committees treats them as a monolith. They're not. The person who signs off on a $500K EDR deployment at a 10,000-person enterprise looks nothing like the IT director evaluating the same tool at a 200-person SaaS company. Company size dictates who's in the room, who holds the budget, and how long the decision takes.
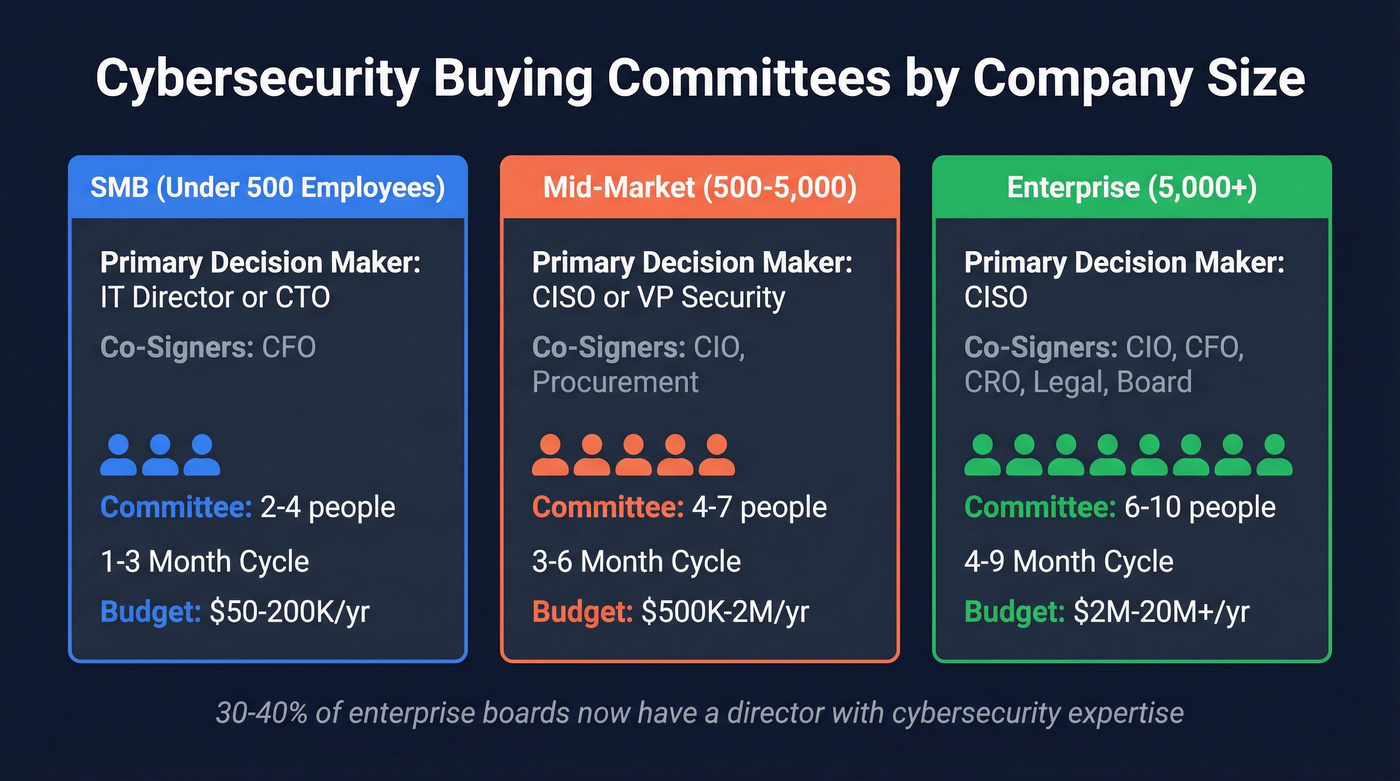
| Segment | Primary Decision Maker | Co-Signers | Committee Size | Typical Cycle | Est. Annual Security Budget |
|---|---|---|---|---|---|
| SMB (<500) | IT Director / CTO | CFO | 2-4 people | 1-3 months | $50-200K |
| Mid-Market (500-5K) | CISO or VP Security | CIO, Procurement | 4-7 people | 3-6 months | $500K-2M |
| Enterprise (5K+) | CISO | CIO, CFO, CRO, Legal, Board | 6-10 people | 4-9 months | $2M-20M+ |
SMB (Under 500 Employees)
No dedicated CISO at most SMBs. The IT Director or CTO wears the security hat alongside infrastructure, helpdesk, and half a dozen other responsibilities. They're evaluating tools themselves, often running free trials before bringing a recommendation to the CFO. Budget sign-off is fast but tight - the CFO wants to know the cost, the risk of not buying, and whether it replaces something they're already paying for.
Mid-Market (500-5,000)
This is where dedicated security leadership emerges - and where we've seen the most deals stall. A CISO or VP of Security owns the strategy, but the CIO co-signs on anything that touches infrastructure. Procurement gets involved for contracts above a certain threshold, and a GRC manager typically weighs in on compliance implications.
Decisions take longer because more people need to agree, but the budgets are real. If you're selling into mid-market, loop procurement in early or watch your deal sit in limbo for months.
Enterprise (5,000+)
Enterprise cybersecurity purchases are committee affairs. The CISO drives the evaluation, but the CIO, CFO, Chief Risk Officer, legal counsel, procurement, and increasingly the board's audit committee all have a voice. Around 30-40% of boards have a director with meaningful cybersecurity background, which helps explain why RAG dashboards persist as the default reporting format - more on why that's a problem later.
EU regulation has raised the governance stakes considerably: under frameworks like NIS2 and sector rules like DORA in financial services, directors and executives face personal accountability for cybersecurity governance failures. Board members who used to rubber-stamp security budgets are now asking pointed questions. Expect 6-10 stakeholders and a sales cycle that can stretch to nine months.
What Security Leaders Care About in 2026
The CISO role has expanded dramatically. Splunk's latest CISO Report found that 96% of CISOs now oversee AI governance and risk across the enterprise. That's a primary responsibility, not a side project. 85% say DevSecOps falls under their purview, and 67% handle IoT/OT/ICS security integrations.
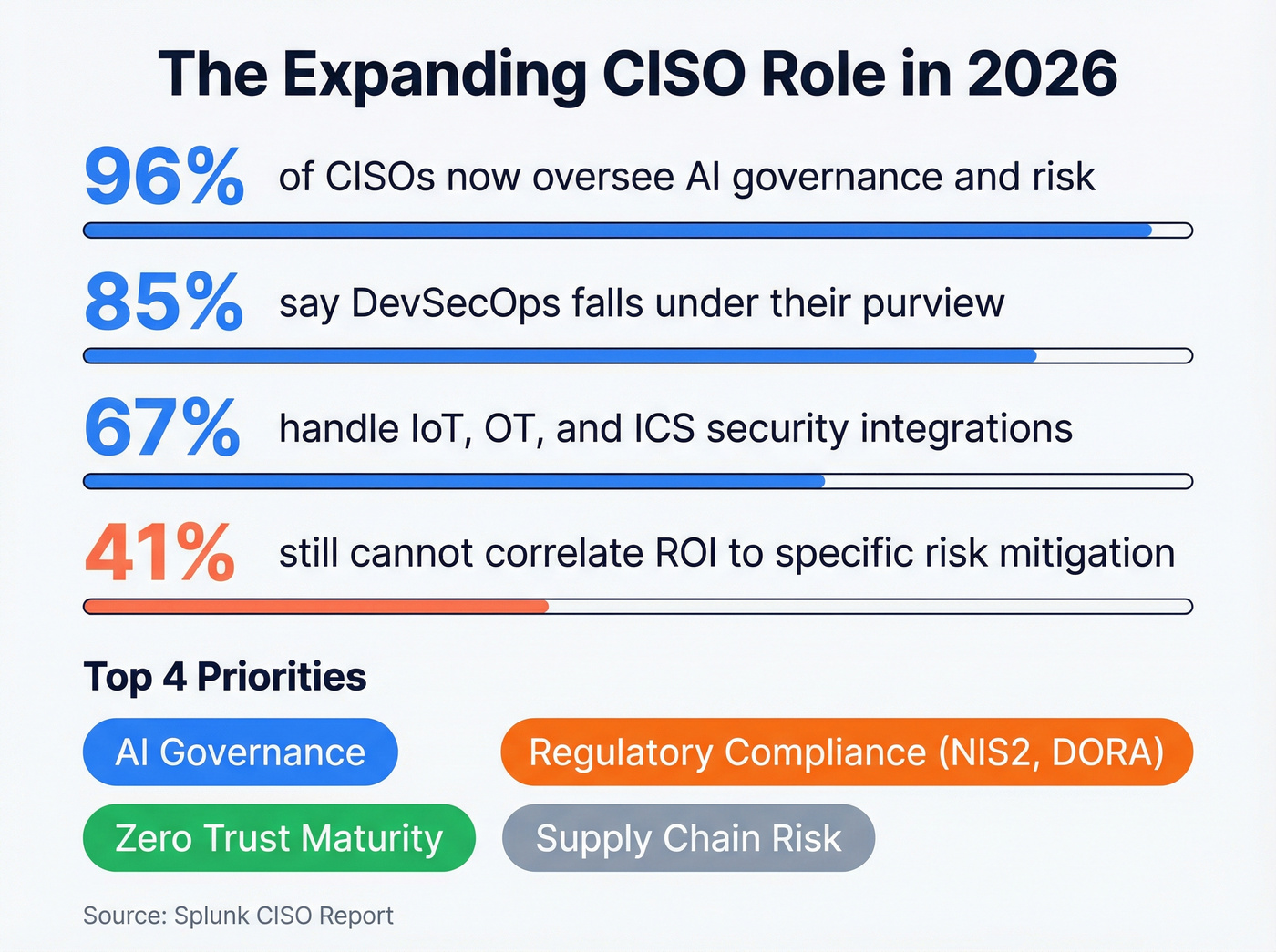
AI governance is the dominant new concern. NIST held a workshop on a preliminary CSF Profile for Artificial Intelligence in January 2026, signaling that AI risk management is being formalized into the same frameworks CISOs already use. If you're selling AI-adjacent security tools, this is the conversation to join.
Regulatory pressure has teeth now. NIS2 raises accountability for cyber governance failures in the EU, and DORA increases governance expectations for financial services. CISOs aren't just managing risk - they're managing legal exposure for their executives.
Zero trust maturity remains a priority, but the conversation has shifted from "should we adopt zero trust" to "how mature is our implementation." Supply chain risk rounds out the top concerns, driven by high-profile incidents that proved third-party vendors are the softest entry point.
How Cybersecurity Decisions Get Made
Governance Frameworks
NIST CSF 2.0 introduced GOVERN as a sixth core function - the most significant structural change in the framework's history. The GOVERN section contains 31 directives, up from just four in the previous version, and it's designed to support organizational risk communication with executives.
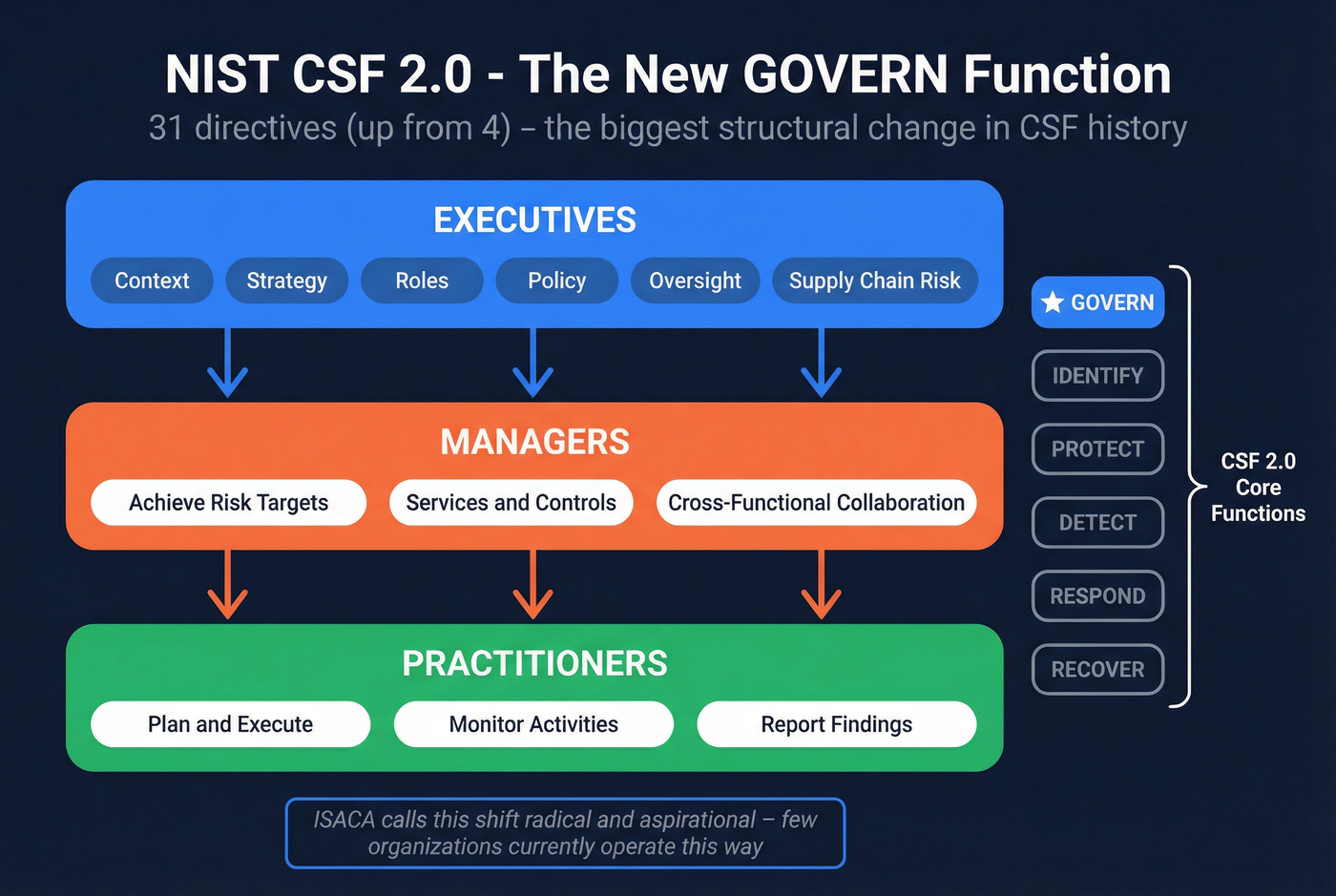
CSF 2.0 frames a clear hierarchy: executives own context, strategy, roles, policy, oversight, and supply chain risk. Managers focus on achieving risk targets through services, controls, and cross-functional collaboration. Practitioners plan, execute, and monitor specific cybersecurity activities. The ISACA Journal calls this shift "radical and aspirational" - and notes that few organizations currently operate this way.
That's the gap vendors should be selling into.
For financial risk quantification, FAIR (Factor Analysis of Information Risk) is the dominant model. Its five principles boil down to: start with a defined risk scenario, don't let perfect data block useful analysis, deliver at the speed of business, include cost-effectiveness, and speak the language of your audience. That last one matters most - FAIR's own guidance uses examples like translating risk into EBITDA impact for M&A stakeholders.
The ROI Math
Cybersecurity ROI is fundamentally a counterfactual problem: you're measuring the value of things that didn't happen. But established formulas make the case concrete.
ALE = SLE x ARO (Annualized Loss Expectancy = Single Loss Expectancy x Annual Rate of Occurrence). This gives you the baseline expected loss.
ROSI = (Risk Exposure x Risk Mitigation % - Cost of Solution) / Cost of Solution. This is how you justify the spend.
The Gordon-Loeb "37% rule" provides a sanity check: invest up to 37% of expected loss to protect an asset. Beyond that, you're likely over-investing relative to the risk.
A worked example: your organization faces a ransomware scenario with an ALE of $100K. You're evaluating an EDR solution that costs $60K/year and reduces that risk by 80%. Post-investment ALE drops to $20K. Your ROSI: ($100K x 0.8 - $60K) / $60K = 0.33, or a 33% return. That's a defensible number in a board presentation.
Yet 41% of security teams still can't correlate ROI to specific risk mitigation activities. The math exists. The discipline to apply it consistently doesn't.

Selling into cybersecurity buying committees means reaching CISOs, CIOs, and security VPs with verified contact data - not bounced emails that torch your domain. Prospeo gives you 98% accurate emails and 125M+ verified mobile numbers with 30+ filters including job title, department headcount, and technographics to pinpoint the exact security leaders at your target accounts.
Stop guessing who owns the security budget. Find them in seconds.
Why Cybersecurity Decisions Fail
Cognitive Biases at the Board Level
A Dutch study covered by Computer Weekly identified seven cognitive biases that undermine board-level cyber decisions: optimism bias, pessimism bias, herding bias, confirmation bias, ambiguity bias, overconfidence bias, and endowment bias.
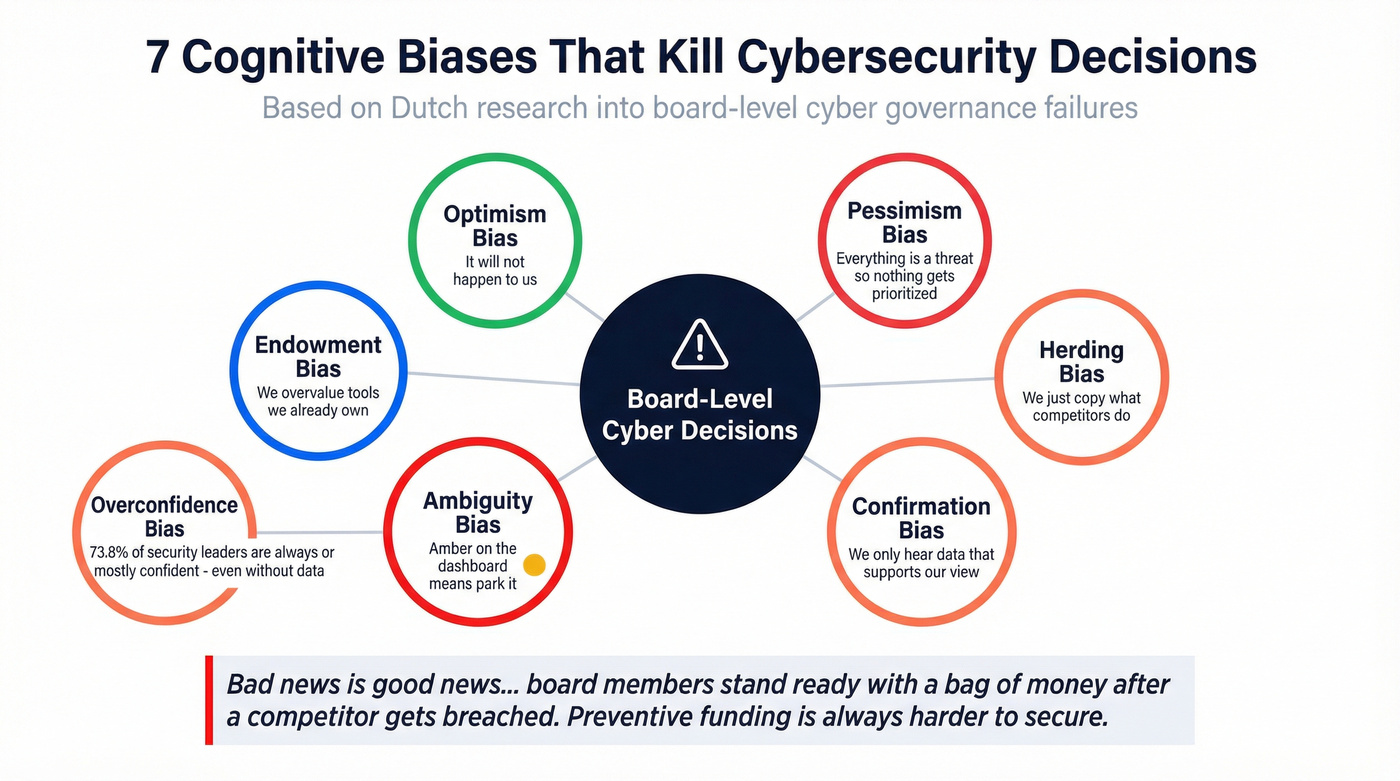
The most insidious is ambiguity bias, and it shows up in every RAG dashboard. When a risk is rated "amber," boards treat it as a parking space - not an action item. Amber means "we acknowledge this exists but aren't going to do anything about it right now." That deferral compounds until amber becomes red, and by then the budget conversation is reactive.
One CISO in the study captured the dynamic perfectly: "Bad news is good news... board members stand ready with a bag of money" after a competitor gets breached. Preventive funding is harder to secure than post-incident funding. That's not rational risk management - it's availability bias in action.
News-driven focus on external breaches causes leaders to downplay internal risks like unpatched systems, employee behavior, and misconfigured controls. The threats that make headlines aren't the threats most likely to hit you.
The Communication Gap
The bias problem is compounded by a communication failure. Ivanti's 2026 report found that nearly 6 in 10 security professionals say their teams are only moderately effective at communicating risk exposure to executive leadership. Only 51% of companies track exposure scores or risk-based indexes.
The metrics security teams do track - MTTR (47%) and percentage of exposures remediated (41%) - don't translate to business impact. Telling the CFO you reduced mean time to remediate by 18% is meaningless without the "so what" in dollar terms.
Here's the thing: security leaders are also overconfident in their own judgment. An ASIS survey of ~170 security decision makers found 73.8% are always or mostly confident in their consequence judgments, and 67.7% are confident in likelihood estimates - even without exact information. Their most trusted sources are fellow experts (76.3%) and peers (56.4%); only 15% said information from higher management is very important. Confidence isn't accuracy. And under NIS2, overconfident risk assessments create real governance exposure.
Communicating Risk to Executives
The CFO asks one question: "What happens to revenue if we don't spend this?" Silence in that moment kills the budget request.
Every risk conversation with executives needs to translate to three things: revenue impact (what's the dollar exposure if this threat materializes), reputation impact (what's the customer and market fallout), and regulatory exposure (what fines, lawsuits, or executive accountability follow).
FAIR's "speak the language of your audience" principle isn't optional - it's the difference between getting budget and getting deferred. When Maersk lost an estimated $300M to NotPetya, the EBITDA impact was the number that resonated in boardrooms worldwide, not the technical details of the attack vector.
Translate Metrics Into Business Language
Most security dashboards report technical metrics. Executives need financial ones.
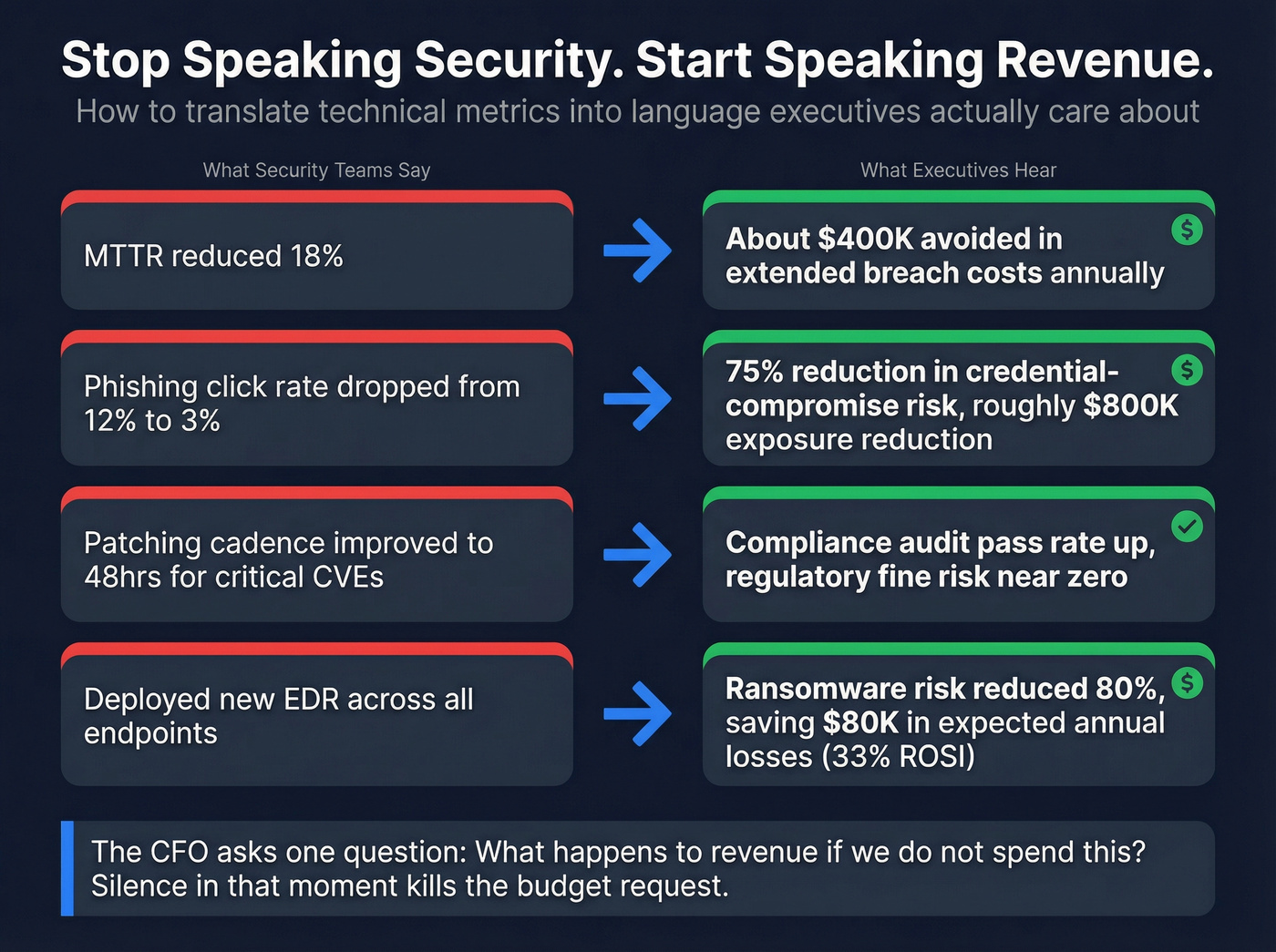
| Security Metric | Executive Translation |
|---|---|
| MTTR reduced 18% | ~$400K avoided in extended breach costs annually |
| Phishing click rate dropped from 12% to 3% | 75% reduction in credential-compromise risk; est. $800K exposure reduction |
| Patching cadence improved to 48hrs for critical CVEs | Compliance audit pass rate up; regulatory fine risk near zero |
| Third-party vendor risk score improved 40% | Supply chain breach probability cut by ~35%; protects partner revenue |
Replace RAG dashboards with quantified ranges. Instead of "amber risk," present "a 15-25% probability of a $2-5M loss event within 12 months." That's actionable. That's something a CFO can weigh against other capital allocation decisions.
Incident reduction remains the top metric - 82% of CISOs use it to communicate security ROI. But pair it with financial impact. "We reduced incidents by 40%" is good. "We reduced incidents by 40%, avoiding an estimated $1.2M in breach costs" is what gets the next budget approved.
Most Teams Target the Wrong Person
Let's be honest about something vendors don't want to hear: if your average deal is under $50K, you probably don't need to reach the CISO at a Fortune 500. That person has 10 vendors in their inbox before breakfast. The IT Director at a 300-person company with a compliance deadline next quarter? That's where your win rate doubles.
Match your outreach to the segment where your deal size makes sense, and stop burning cycles on logos that look good on a slide deck.
For teams selling to CISOs at large enterprises, you need a fundamentally different playbook - longer nurture sequences, multi-threaded outreach across the buying committee, and messaging that speaks to governance and board-level accountability rather than feature comparisons. The consensus on r/cybersecurity is that cold emails pitching "AI-powered" anything to a CISO without referencing their specific risk context get deleted instantly. Context is the price of admission.
How to Find and Reach Security Buyers
We've run outbound campaigns where a huge chunk of "CISO" lists turned out to be stale - emails bounced, people had changed roles, and the messaging missed the risk conversation entirely. That's not prospecting. That's domain reputation suicide.
Reaching cybersecurity decision makers requires three things. First, accurate titles - "CISO" at a 200-person company means something different than at a 20,000-person enterprise. Second, verified contact data, because stale emails destroy deliverability. Third, timing signals, because reaching a security leader during a compliance deadline or after a funding round is fundamentally different than reaching them on a random Tuesday.
Prospeo covers 300M+ professional profiles with 30+ search filters, including buyer intent across 15,000 topics powered by Bombora, technographic signals for companies running specific security stacks, and job change alerts so you know when a new security leader lands and is actively evaluating vendors. Email accuracy runs at 98% with a 7-day data refresh cycle, compared to the industry average of six weeks. Snyk's team of 50 AEs cut bounce rates from 35-40% to under 5% after switching, generating 200+ new opportunities per month - the difference between a campaign that builds pipeline and one that gets your domain blacklisted.
Skip this approach if you're only targeting a handful of named accounts. For five or ten companies, manual research works fine. But the moment you're building lists of 100+ security leaders across a segment, you need a data platform that doesn't feed you dead emails.
The self-serve model starts free - 75 verified emails per month plus 100 Chrome extension credits, no contracts, no sales calls required.

Enterprise security deals involve 6-10 stakeholders and 9-month cycles. You can't afford to waste months chasing outdated contacts. Prospeo refreshes every 7 days - not the 6-week industry average - so the CISO who just changed companies last week is already in your search results. At $0.01 per email, mapping an entire buying committee costs less than a cup of coffee.
Build the full security buying committee before your competitors find the CISO.
FAQ
Who is the primary cybersecurity decision maker at most companies?
At enterprises with 5,000+ employees, the CISO holds primary authority. At SMBs under 500, the IT Director or CTO owns security alongside other responsibilities. Budget sign-off typically requires CFO approval regardless of company size, and mid-market deals usually need CIO co-sign.
How many stakeholders join a security buying decision?
Enterprise purchases involve 6-10 stakeholders spanning security, IT, procurement, legal, and finance, with sales cycles running 4-9 months. Mid-market committees are smaller at 4-7 people but still multi-threaded. SMB deals close fastest with 2-4 people involved.
What frameworks guide cybersecurity buying decisions?
NIST CSF 2.0 provides governance structure - its new GOVERN function added 31 directives for executive-level risk communication. FAIR handles financial quantification, translating threats into dollar-denominated loss expectancy that CFOs can evaluate against other investments.
What do CISOs prioritize in 2026?
AI governance tops the list - 96% of CISOs now oversee it as a primary responsibility. DevSecOps ownership follows at 85%, OT/IoT security at 67%, and regulatory compliance under NIS2 and DORA. Zero trust maturity and supply chain risk round out the top concerns.
How can I build a verified list of security leaders?
Use a B2B data platform with title-level filtering, technographic signals, and buyer intent data. Prospeo's database lets you filter by security-specific job titles, company tech stack (e.g., companies running CrowdStrike or Palo Alto), and intent topics like "endpoint detection" or "zero trust" - then delivers 98%-accurate emails refreshed every 7 days. The free tier includes 75 verified contacts per month.

