Best OSINT Email Lookup Tools in 2026 (Tested)
You've got an email address from a phishing report, a fraud investigation, or a due diligence request. You have 30 minutes. The email could be spoofed, a burner, or the thread that unravels an entire network. The tools you reach for in that window determine whether you get actionable intelligence or a dead end.
Email addresses decay at roughly 3.6% per month. Companies lose an estimated $12.9M annually from decisions built on bad data. And most "OSINT tool" roundups dump 30 options with no pricing, no workflow, and no opinion on what actually works. That's a homework assignment, not a guide.
Our Picks
| Category | Tool | Why |
|---|---|---|
| Email finding & verification | Prospeo | 98% accuracy, 7-day refresh, free tier |
| Account enumeration | user-scanner | Free, open-source, actively maintained |
| Breach & darknet search | IntelX | 200B+ records, free tier with 50 searches/day |
| Domain email discovery | Hunter.io | Bulk domain search, 50 free credits/month |
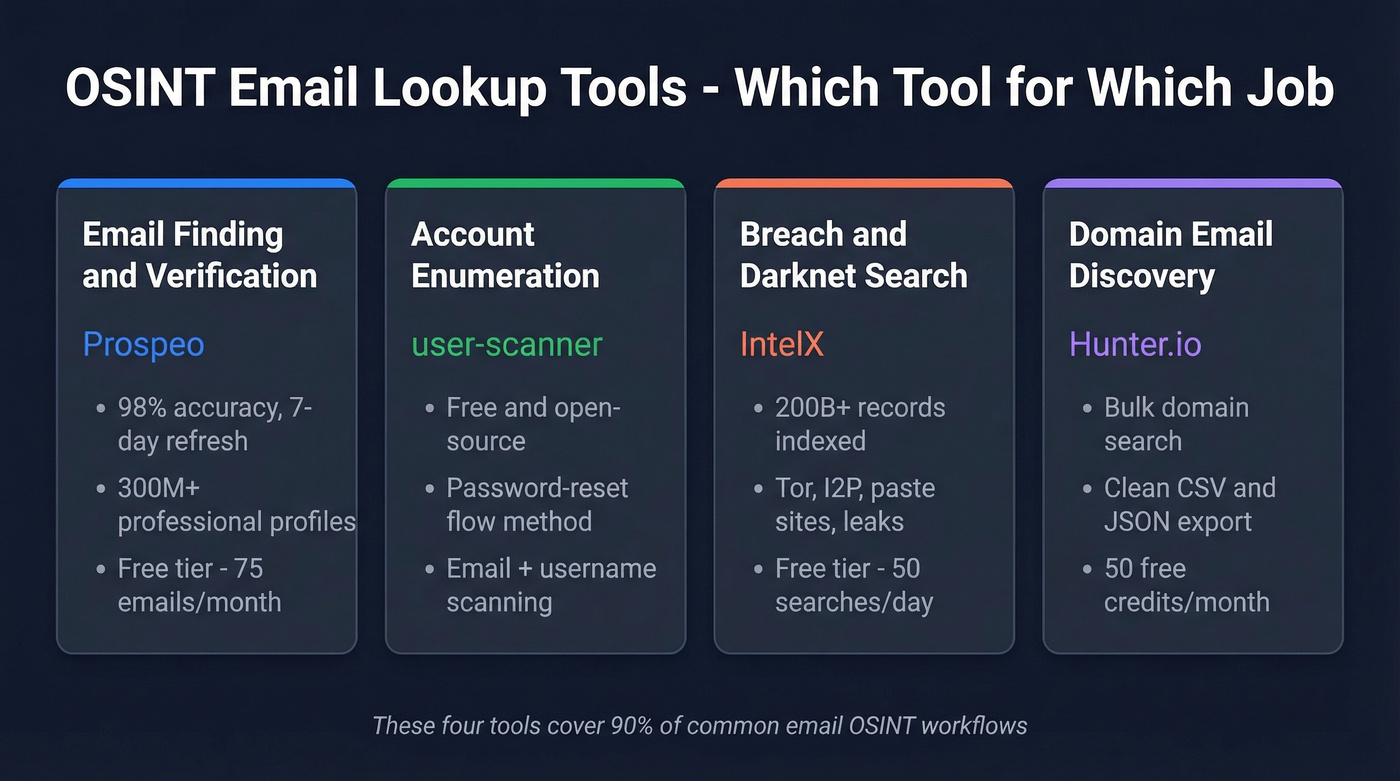
These four handle 90% of common email OSINT workflows. The rest of this article fills in the edges - breach checks, header analysis, reverse lookups - plus a step-by-step investigation framework we've used on real engagements.
How to Choose the Right Tool
What's your actual task? Finding emails, verifying them, enumerating accounts, and searching breach data are different jobs requiring different tools. Don't reach for a breach database when you need a verified contact.
Coverage and depth aren't the same thing. A tool that checks 140 services shallowly isn't better than one that checks 40 deeply. Anonymity matters too - does the tool alert the target or log your queries? And if the GitHub repo hasn't seen a commit in over a year, move on. Many tools in popular OSINT guides have broken modules that'll waste your time before you even realize the results are garbage.
Think about output format and cost at scale. JSON and CSV exports matter when you're feeding results into other tools. Free works for single lookups; bulk investigations need credit-based pricing that won't bankrupt you.
Manual Email Analysis First
Before firing up any tool, spend two minutes reading the email address itself.
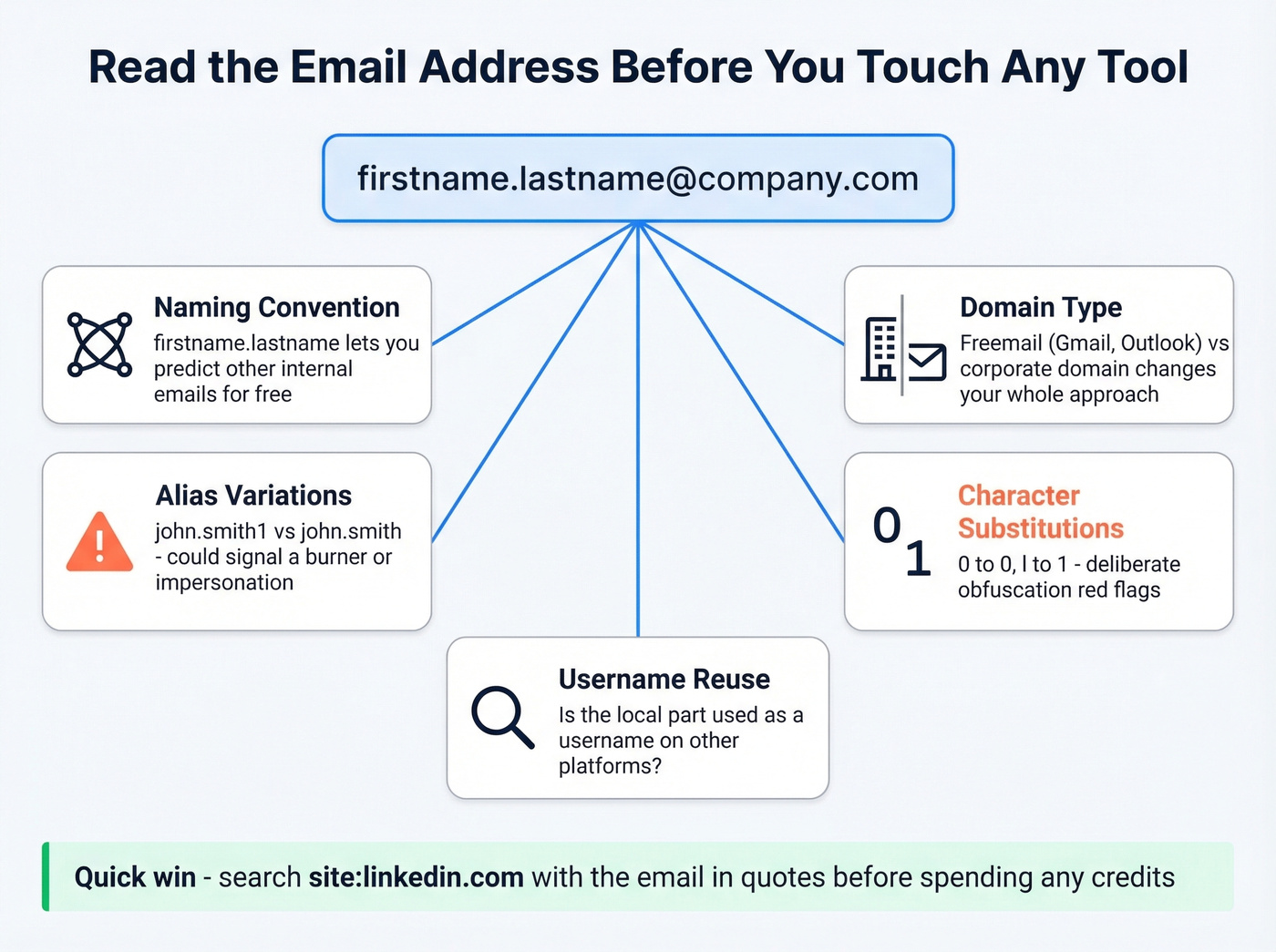
A firstname.lastname@company.com pattern lets you predict other internal emails immediately - that's free pivot material. Watch for alias variations: john.smith1@ versus john.smith@ can indicate a burner or impersonation attempt. Check whether the local part is reused as a username elsewhere, and look for character substitutions like O→0 or l→1 that suggest deliberate obfuscation. Freemail domains like Gmail or Outlook versus a corporate domain will change your entire investigation approach.
A quick "john.smith@company.com" site:linkedin.com or intext:"john.smith@company.com" costs nothing and often surfaces public mentions before you spend a single credit.

Most OSINT email tools work off data that's weeks or months old - and at 3.6% monthly decay, that means dead leads and wasted investigation time. Prospeo's 7-day refresh cycle and 98% email accuracy give you verified, deliverable addresses when the clock is ticking.
Stop chasing bounced emails. Start with data you can act on.
Best Tools for Email OSINT
Prospeo - Email Finding & Verification
Most OSINT tools tell you an email exists. Prospeo tells you it's verified, deliverable, and current. That distinction matters when acting on a dead email wastes time and burns your domain reputation.
The database covers 300M+ professional profiles with 143M+ verified emails, all refreshed on a 7-day cycle - the industry average sits around six weeks, which is an eternity in OSINT. Email accuracy runs at 98%, backed by a 5-step verification process that includes catch-all handling, spam-trap removal, and honeypot filtering. We've seen practitioners burn hours chasing addresses that bounced because their verification tool was working off stale data; that's the problem a weekly refresh solves. If you need a deeper breakdown of verification methods, see our guide on how to check if an email exists.
The Chrome extension with 40,000+ users lets you pull verified emails from professional profiles and company websites in one click. For bulk work, upload a CSV and get results in minutes. The free tier gives you 75 emails/month; paid plans run about $0.01/email. If you're comparing verifiers, our roundup of email verification options is a good next read.
IntelX - Breach & Darknet Search
€2,500/year for the entry-level paid tier. That's the first thing you should know about Intelligence X, because it tells you exactly who this tool is for.
IntelX searches across 200B+ records spanning paste sites, darknet services on Tor and I2P, Wikileaks, Cryptome, data leaks, Whois records, and the public web. You can search by email, domain with wildcards, URL, IP/CIDR, phone number, or crypto address. No other tool in this category matches that breadth of selector types.
The free tier gives you 50 searches per day - enough for individual investigations. The Researcher tier at €2,500/year bumps that to 200 searches/day. Mid-tier plans at €7,000 and €10,000/year bridge the gap to Enterprise at €20,000/year with 5,000+ daily searches.
Skip this if you just need to find or verify professional emails. That's not what IntelX is built for.
user-scanner - Account Enumeration
Holehe is in every OSINT guide on the internet, and many of its modules are outdated or broken. user-scanner is the maintained successor. Here's how fast you can get started:
pip install user-scanner
user-scanner -e "target@example.com" -v
For bulk work: user-scanner -ef emails.txt -o results.json
It combines email and username scanning into a single tool, checking whether an email is registered across dozens of services using password-reset flow enumeration - the same methodology Holehe popularized, but with actively maintained modules and proxy validation. In our testing, we've watched practitioners waste hours troubleshooting Holehe's false negatives when user-scanner gives clean results in minutes.
Skip this if you need email finding or breach data. Different tools, different jobs.
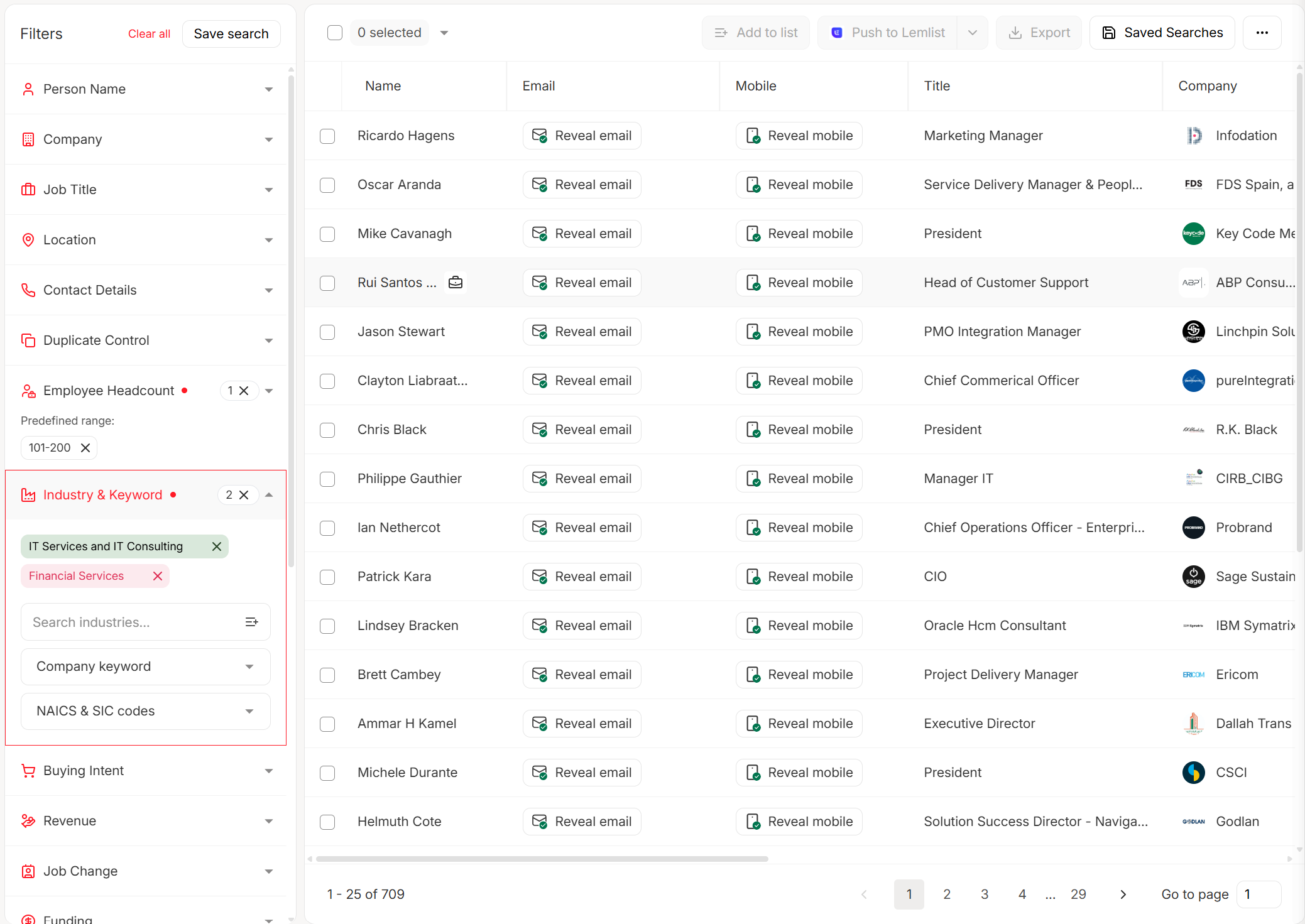
Hunter.io - Domain Email Discovery
Hunter is a sales tool that OSINT practitioners have adopted - and that's fine. Give it a company domain and it returns every email pattern and address it can find. If you're evaluating similar tools, check our tested list of Hunter alternatives.
| Pros | Cons | |
|---|---|---|
| Coverage | Strong on corporate domains | Weak on freemail/personal |
| Pricing | 50 free credits/month; Starter $49/mo ($34/mo yearly) | Credits burn fast on large orgs |
| Output | Clean CSV/JSON, API access | No breach or darknet data |
One credit finds one email; half a credit verifies one. Bulk domain search costs one credit for up to 10 emails per domain, making it efficient for mapping organizational email structures.
Epieos - Reverse Email Lookup
Epieos checks an email against 140+ services - Google, Skype, Pinterest, Gravatar, Strava, Trello, and more - and returns linked accounts. It integrates with Maltego for relationship graphing and runs stealth searches that don't rely on breached databases.
Here's the thing: the Reddit consensus on r/OSINT is blunt. Results are "pretty minimal most of the time." At ~$32/month, that's a tough sell when user-scanner does account enumeration for free. Skip this if you need comprehensive results - the price-to-value ratio doesn't hold up for most investigators.
Quick Mentions
HIBP (Have I Been Pwned) - The go-to breach check for individual lookups. Free, fast, and Troy Hunt keeps it current.
Dehashed - Breach database with wildcard support, typically ~$10-$30/month. More granular than HIBP for searching partial emails, usernames, or IPs across leaked datasets.
MXToolbox - Free email header analysis. Paste raw headers and get SPF/DKIM/DMARC checks plus relay information. Essential for phishing investigations. If you want to go deeper on authentication signals, see DMARC alignment and SPF record examples.
Phonebook.cz - Free email and domain search. Surprisingly capable for initial recon when mapping a domain's email footprint.
ThatsThem - Free reverse email lookup returning associated identity and contact details from public records. US-focused, limited internationally.
TheHarvester - Free, open-source Python tool that scrapes emails, subdomains, and IPs from search engines, PGP servers, and Shodan. A staple in OSINT toolkits for good reason.
GHunt - Free Google account OSINT. If the target email is a Gmail address, GHunt can pull associated Google services and profile photos. For Gmail-specific checks, see how to check if a Gmail account exists.
SEON - Fraud-focused email intelligence starting around $100/month. Checks a wide set of social and digital signals per email. Worth knowing if your OSINT work overlaps with fraud investigation.
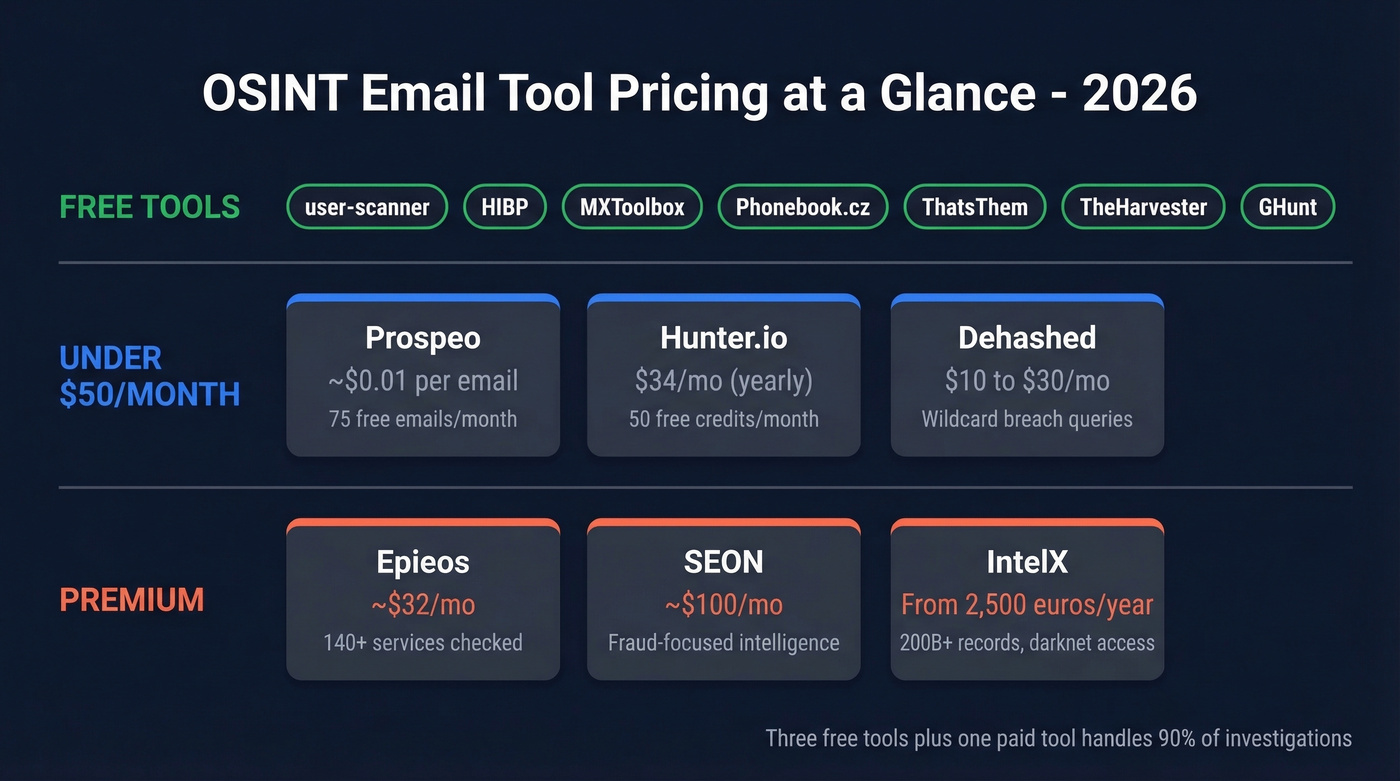
Pricing Comparison
| Tool | Free Tier | Paid From | Best For |
|---|---|---|---|
| Prospeo | 75 emails/mo | ~$0.01/email | Verified professional emails |
| IntelX | 50 searches/day | €2,500/yr | Deep breach investigations |
| Hunter.io | 50 credits/mo | $34/mo (yearly) | Org email mapping |
| Epieos | Limited | ~$32/mo | Quick identity checks |
| user-scanner | Unlimited | Free | Registration checks |
| HIBP | Yes | Free (API paid) | Breach exposure checks |
| Dehashed | Limited | ~$10-$30/mo | Wildcard breach queries |
| MXToolbox | Unlimited | Free | Header forensics |
| Phonebook.cz | Unlimited | Free | Email/domain recon |
| ThatsThem | Unlimited | Free | Reverse lookup (US) |
| TheHarvester | Unlimited | Free | Multi-source scraping |
| GHunt | Unlimited | Free | Google account OSINT |
| SEON | Limited | ~$100/mo | Fraud email intelligence |
Stop Hoarding Tools
Most OSINT practitioners collect tools like trading cards. They install 15 packages, sign up for 8 platforms, and still can't answer a basic question about a single email address in under 30 minutes. Three tools - one for enumeration, one for breach data, one for verification - handle 90% of investigations. Everything else is edge-case insurance. Build depth with fewer tools rather than breadth with many. If you're building a broader stack, our list of free lead generation tools also includes several email-focused utilities.
Investigation Workflow
Let's walk through the phishing report scenario from the intro. You've got a suspicious email and 30 minutes.
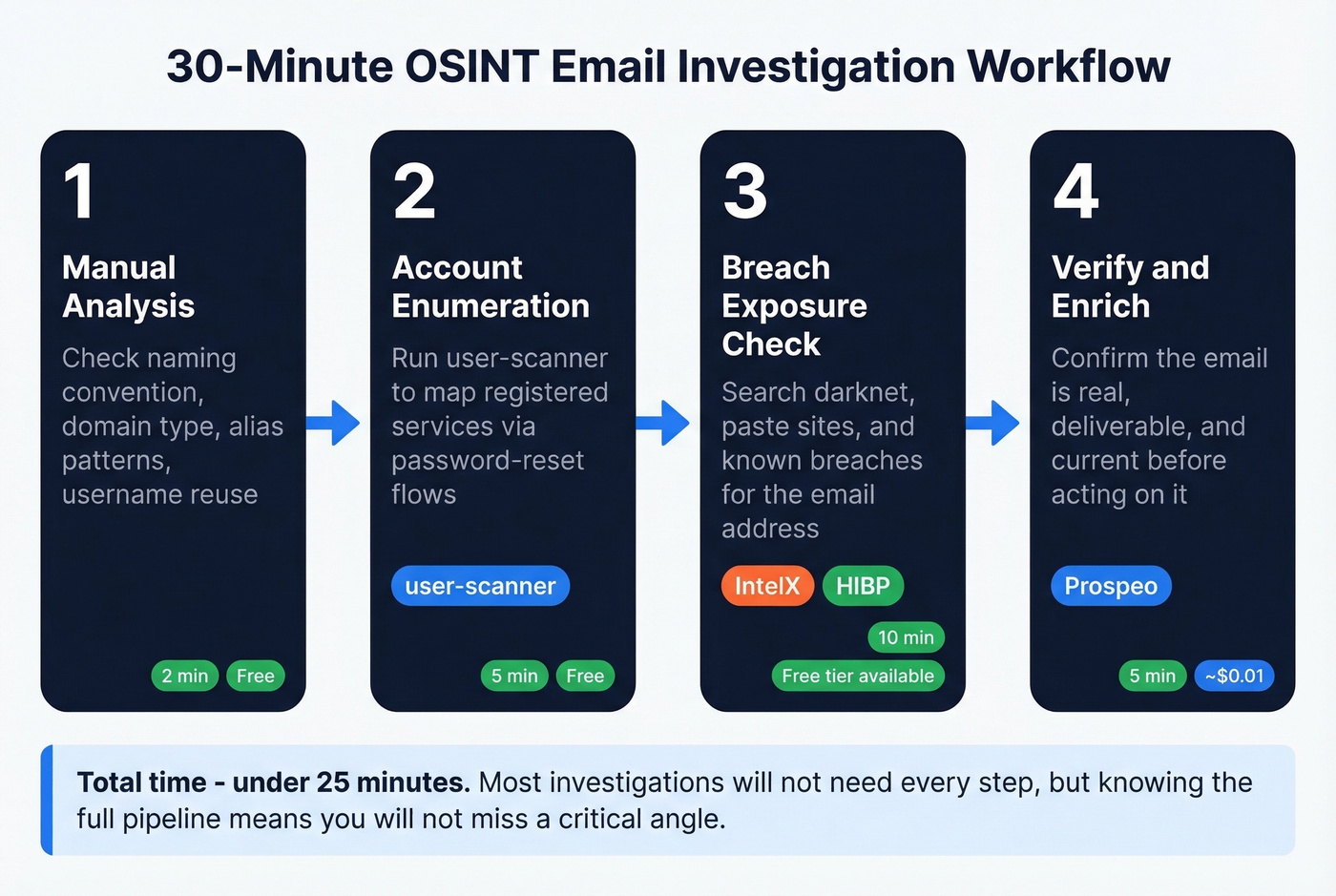
1. Analyze the email manually. Check naming convention, domain type, alias variations, and username reuse patterns. Two minutes, zero cost.
2. Enumerate accounts with user-scanner. Run user-scanner -e "suspect@domain.com" -v to map which services the email is registered on. user-scanner doesn't send emails to the target since it uses password-reset flow enumeration, so you won't tip anyone off.
3. Check breach exposure with IntelX and HIBP. IntelX searches darknet and paste sites; HIBP confirms known breach appearances. Together they give you a complete picture of breach exposure. If both come back empty, that's a data point too - it suggests a newer or more carefully managed address.
In our experience, this four-step sequence consistently surfaces intelligence that single-tool approaches miss. Most investigations won't need every step - but knowing the full pipeline means you won't miss a critical angle when it matters.

Before you burn credits on breach databases or enumeration tools, verify the email is real. Prospeo's 5-step verification catches spam traps, honeypots, and catch-all domains - the noise that derails investigations. 75 free lookups per month, no contract required.
Verify first, investigate second. 75 free emails are waiting.
FAQ
Is OSINT email lookup legal?
Yes, when you're using publicly available data and legitimate tools. Accessing breach databases is restricted or illegal in some jurisdictions, and GDPR applies when investigating EU subjects. Always check local laws before starting - especially with darknet or breach data sources.
Can I run email investigations for free?
Absolutely. user-scanner, Phonebook.cz, TheHarvester, ThatsThem, and MXToolbox are completely free. Prospeo offers 75 free emails/month and Hunter.io gives 50 free credits. Paid tools like IntelX unlock deeper breach and darknet data, but the free stack handles most routine investigations without spending a dime.
What's the difference between email finding and reverse email lookup?
Email finding discovers an address from a name and company. Reverse lookup takes a known email and maps it to accounts, identities, and breach exposure. Different tools, different use cases - Prospeo and Hunter handle finding, while user-scanner and Epieos handle reverse lookups. If you're doing name-based discovery, our name to email guide breaks down the fastest workflows.