What Is Email Scraping - And Why Most Scraped Emails Are Wrong
Independent testing shows only 38% of emails found by lookup tools are actually correct. The other 62% are wrong or not found. If you're wondering what email scraping really is and whether it's worth the effort, here's the short version: scraping raw emails off websites and blasting cold outreach without verification isn't outreach. It's spam. And the legal environment has gotten sharper - France's CNIL fined KASPR €240,000 for collecting professional contact data without appropriate consent.
Email scraping pulls addresses off websites using automated bots. It's fast, cheap, and produces terrible data. If you need B2B emails for outreach, skip the scraper and use a verified database with 98% email accuracy instead.
How Email Scraping Works
Email scraping is the automated extraction of email addresses from websites, documents, social media profiles, forums, and other public web sources. A bot crawls pages, identifies anything matching an email pattern, and dumps it into a spreadsheet. No verification. No context. No guarantee the address belongs to the person you want to reach.
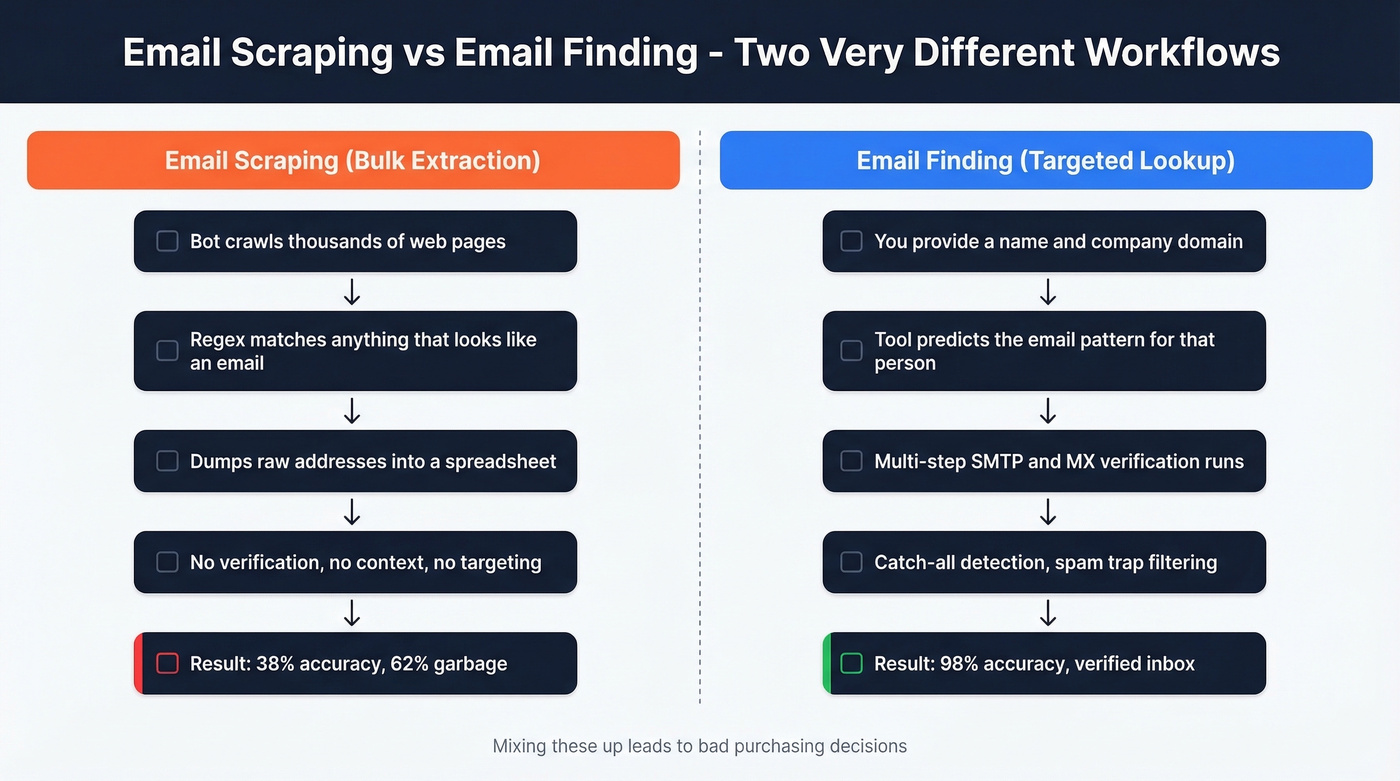
The taxonomy matters because "scraping" gets conflated with two different things. Scrapers are bulk shotgun extraction - crawl a thousand pages, harvest every address you can find. Email finders are targeted lookups - you provide a name and domain, and the tool predicts and verifies a specific person's work email. These are fundamentally different workflows with fundamentally different accuracy profiles, and mixing them up leads to bad purchasing decisions.
Technical Anatomy of a Scraper
A scraper visits a URL or crawls an entire domain, scans the HTML source for anything matching an email pattern, extracts matches, deduplicates, and exports to CSV. The core is a regex pattern matching the standard email format:
[a-zA-Z0-9._%+-]+@[a-zA-Z0-9.-]+\.[a-zA-Z]{2,}
Common scraping stacks include Phantombuster, Outscraper, Apify actors, and Firecrawl - often chained with enrichment layers like Clay. But the blockers are real. Many sites encode email addresses as HTML entities, render them via JavaScript after page load, or hide them behind CAPTCHAs and anti-bot fingerprinting. At scale, IP rate limiting forces scrapers to rotate through residential proxies, adding cost and complexity to what's supposed to be a "free" data source.
If you're comparing tools and workflows, it helps to separate email crawlers from targeted finders and verification.
The Accuracy Problem
Finding emails is easy. Finding correct ones is hard.
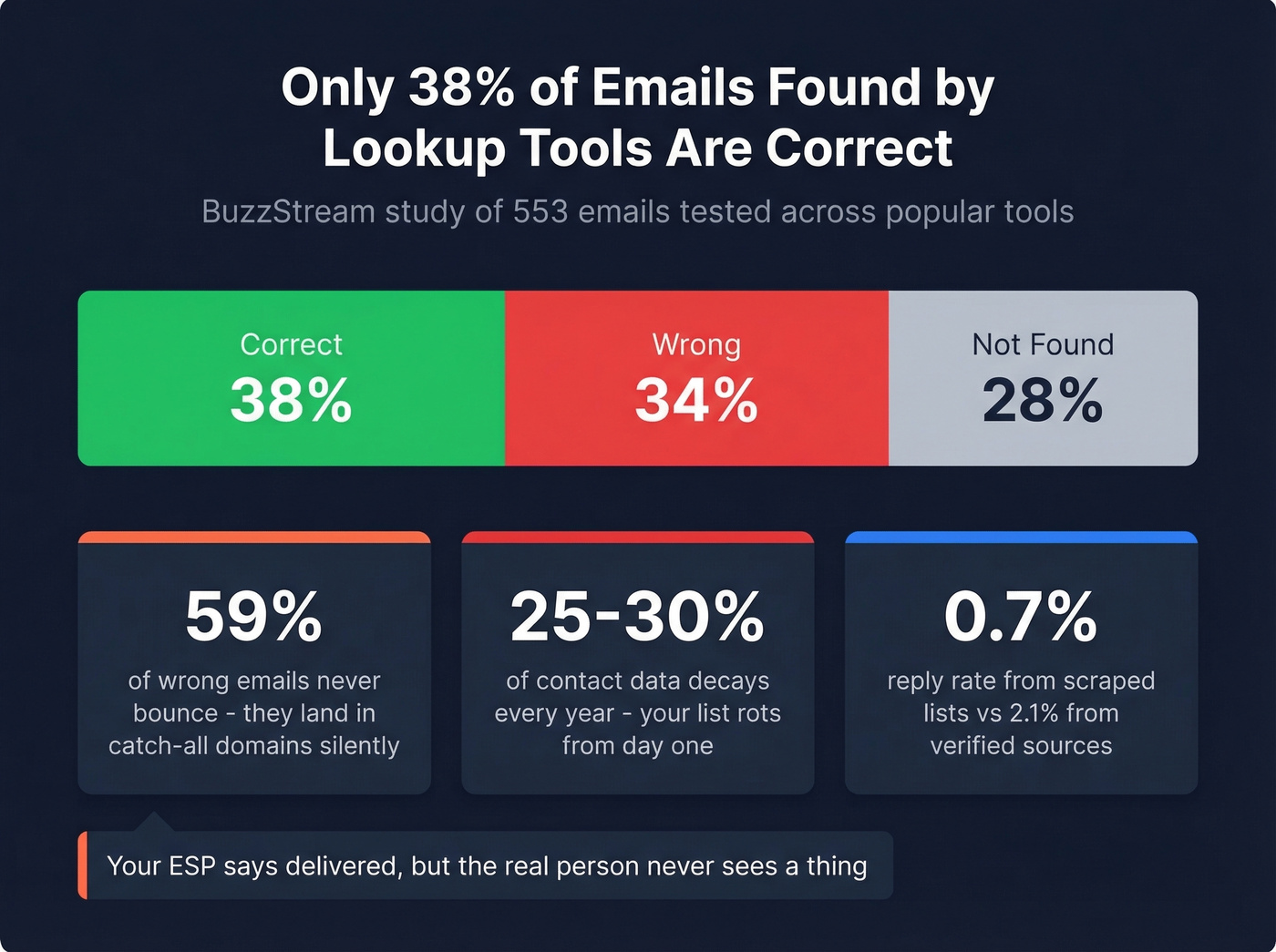
A BuzzStream study tested 553 emails found by email lookup tools. Only 38% were correct. 34% were flat-out wrong, and 28% returned "not found." Here's the part that really stings: 59% of the wrong emails never bounce. They land in catch-all domains that accept everything, so your ESP reports them as "delivered" while the actual person never sees a thing.

One cold email operator on r/coldemail who ran 464K emails across clients reported scraping 330K leads from competitor social pages. After dedupe and qualification, only 150K had valid emails - and reply rates from scraped lists hit 0.7%, compared to 2.1% from Apollo. Contact data decays 25-30% annually, so even a "fresh" scraped list starts rotting the day you build it.
In our experience, the cost math always favors verified data. Scraping runs $0.01-$0.10 per record. But when your list is 62% garbage, that $0.01/record is really about $0.026 per usable contact - before you factor in email deliverability damage, domain warm-up costs, and the hours your SDR spends chasing dead addresses.
If you want to quantify list quality, start with email bounce rate benchmarks and remediation.

Scraped lists average 38% accuracy. That means 62% of your outreach hits dead ends, catch-all traps, or strangers. Prospeo's 5-step verification delivers 98% email accuracy across 143M+ addresses - refreshed every 7 days, not rotting the moment you export.
Stop scraping garbage. Start sending to verified inboxes.
Is Email Scraping Legal?
Let's be honest: the "public data = fair game" argument doesn't hold up anymore.
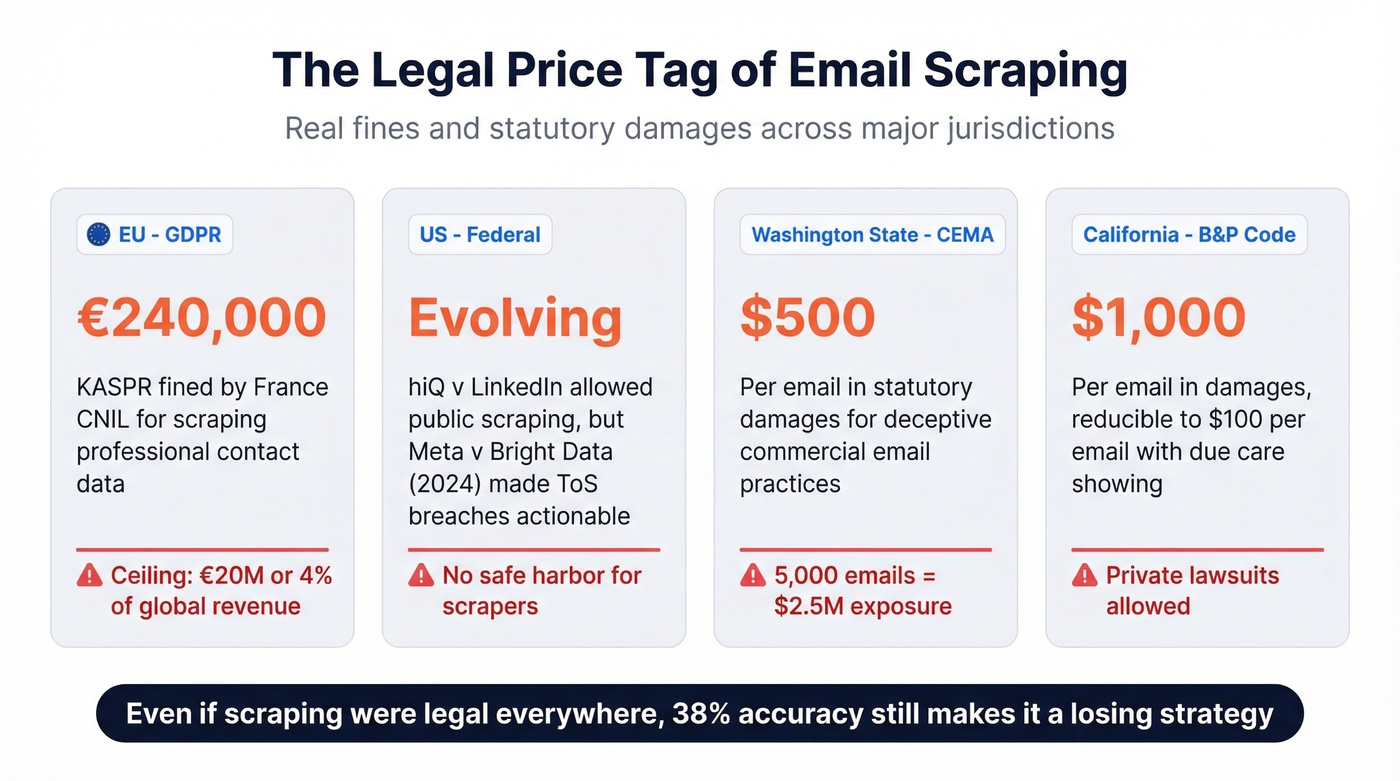
France's CNIL hit KASPR with €240,000 for collecting professional contact data without appropriate consent - even though the data was publicly visible on professional profiles. Under GDPR, the penalty ceiling is €20M or 4% of global annual revenue, whichever is higher.
In the US, courts are tightening too. The hiQ v. LinkedIn case established that accessing publicly available data without bypassing authentication may not violate the CFAA. But Meta v. Bright Data (2024) showed that ToS breaches are actionable even for public content. State laws fill the gap aggressively. Washington's CEMA allows $500 per email in statutory damages for deceptive commercial email practices. California's B&P Code §17529.5 enables private lawsuits where per-email damages are often pled at $1,000 per email and can be reduced to $100 per email with a "due care" showing. Scrape 5,000 emails, send a campaign with a misleading subject line, and you're looking at seven-figure exposure.
If you're weighing risk, it's also worth reading up on whether it is illegal to buy email lists in your jurisdiction and use case.
Here's the thing: regulation isn't what will kill email scraping. The data quality will. Even if every jurisdiction legalized it tomorrow, a 38% accuracy rate makes it a losing strategy for any team that cares about pipeline.
What Happens When You Email a Scraped List
We've seen teams burn their sending domains in a single campaign from scraped lists. The scenario is always the same: your SDR scrapes 5,000 emails from conference attendee pages, loads them into a sequencing tool, and launches. Bounce rate hits 12%. Spam complaints spike. The ESP suspends the account. Rebuilding sender reputation takes 4-8 weeks - and that's if you catch it before the domain gets blacklisted entirely.
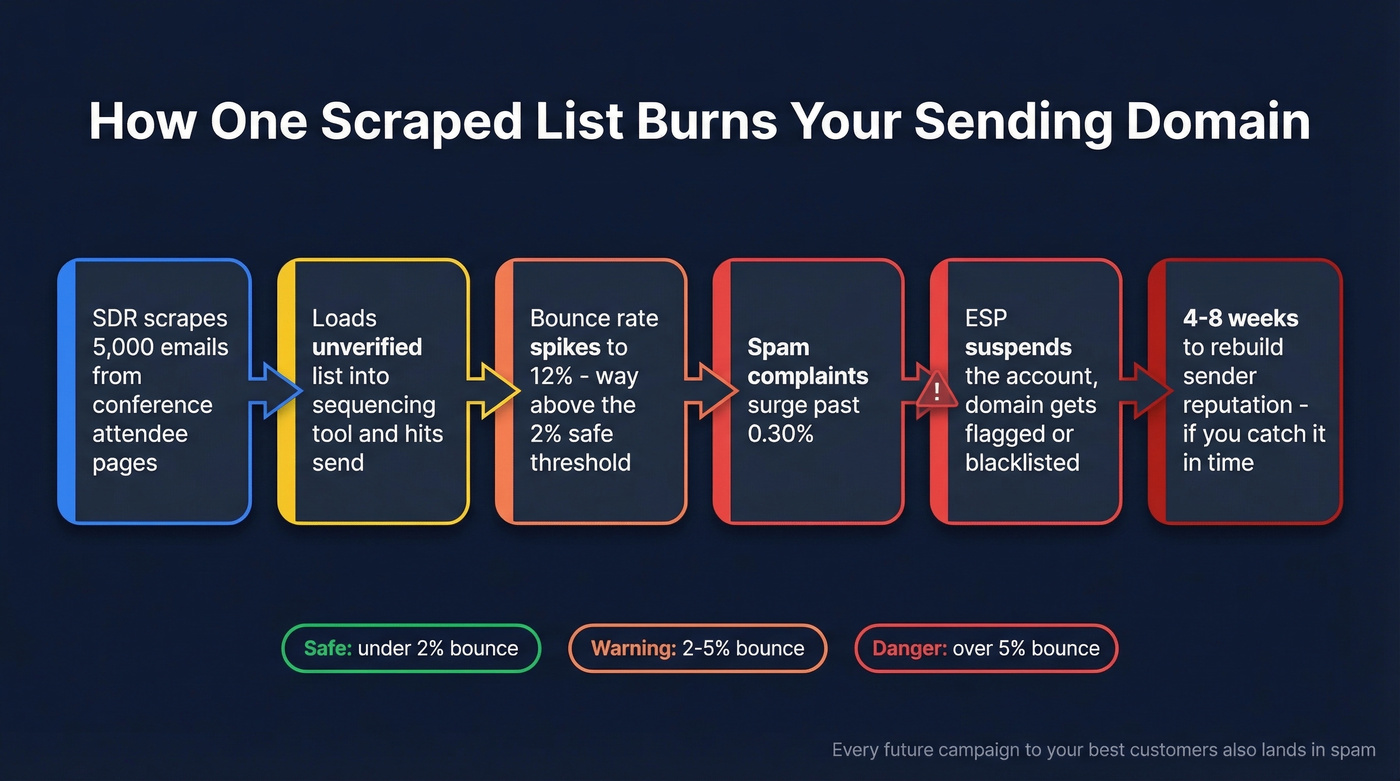
| Metric | Excellent | Warning | Danger |
|---|---|---|---|
| Hard bounce | <2% | 2-5% | >5% |
| Spam complaints | <0.10% | 0.10-0.30% | >0.30% |
| Open rate | >20% | 15-20% | <15% |
Most email marketing platforms explicitly prohibit scraped lists. A 12% bounce rate doesn't just hurt one campaign. It poisons your entire sending domain, which means every future campaign - even to your best customers - lands in spam.
To reduce long-term damage, follow a structured plan to improve sender reputation and monitor with email reputation tools.
The Smarter Alternative
Scraping solves the wrong problem. The bottleneck in outbound isn't finding email addresses. It's finding correct, verified ones that reach the person you actually want to talk to.
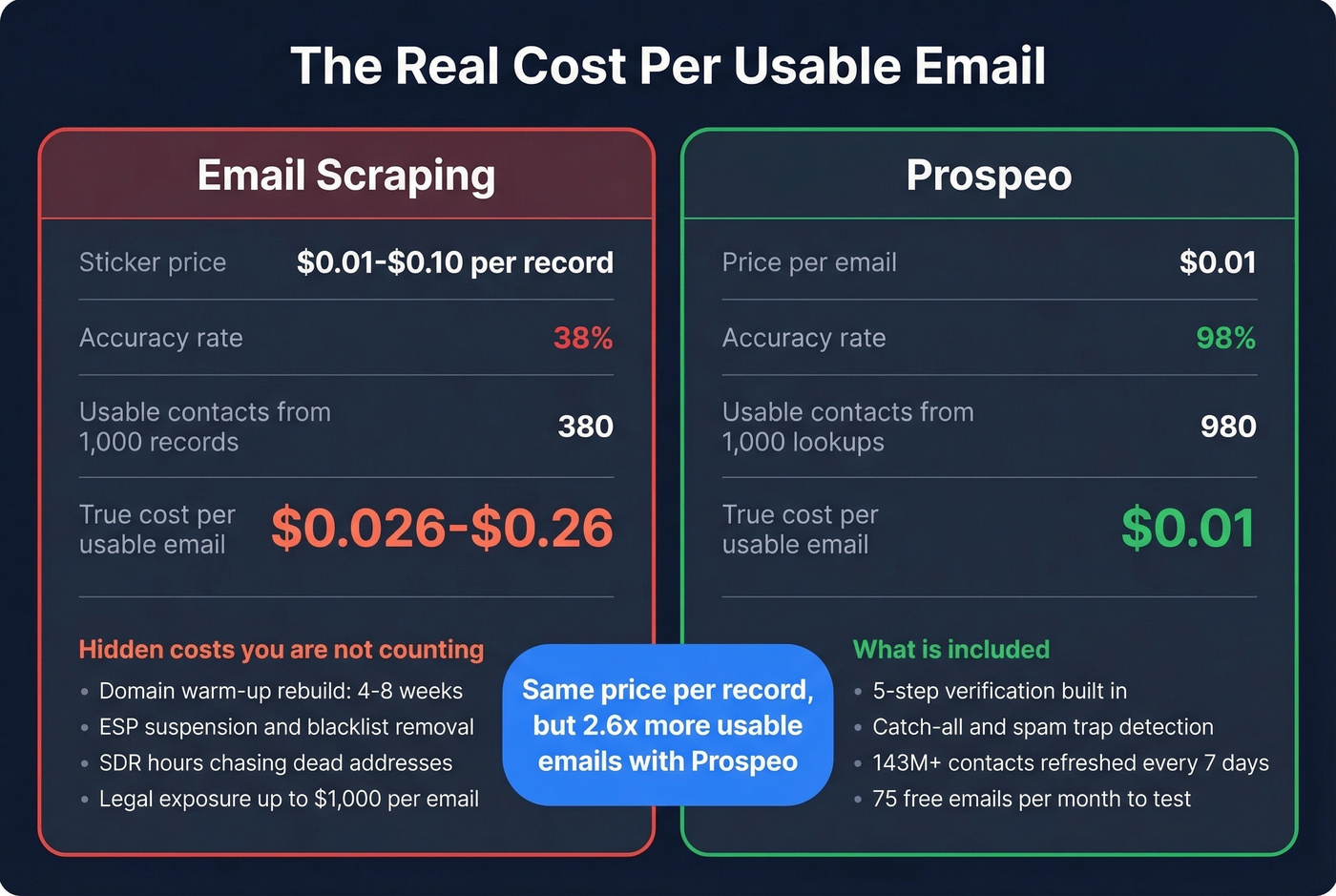
Skip scraping entirely if you care about deliverability, legal exposure, or your team's time. Scraping costs $0.01-$0.10/record at roughly 38% accuracy. Prospeo runs about $0.01/email at 98% accuracy. The free tier gives you 75 emails/month to test - no contract, no sales call.
If you're building outbound from scratch, use a repeatable lead generation workflow and add data enrichment services only after you’ve validated ICP fit.

Email scraping costs $0.01-$0.10 per record but only 38% are usable - that's $0.026+ per real contact before you count domain damage. Prospeo delivers verified emails at $0.01 each with 98% accuracy. No scraping, no legal risk, no bounced domains.
Pay less per email and actually reach the right person.
FAQ
Is email scraping the same as email harvesting?
Yes, the terms are interchangeable - both mean automated extraction of email addresses from web sources. The real distinction is between scraping/harvesting (bulk extraction) and email finding, which targets a specific person by name and domain and verifies the result before returning it.
Can I scrape emails from Google search results?
Technically possible, but Google blocks automated queries with CAPTCHAs and rate limits. Emails found this way are unverified and still roughly 62% wrong. You're adding complexity for garbage data.
How do I verify scraped emails before sending?
Run them through a verification service that checks MX records, SMTP responses, and catch-all domain behavior. A verified database with built-in 5-step verification - covering spam-trap and honeypot removal - lets you skip the scrape-then-verify workflow entirely.