Cyber Security Sales: The Insider's Career & Selling Guide for 2026
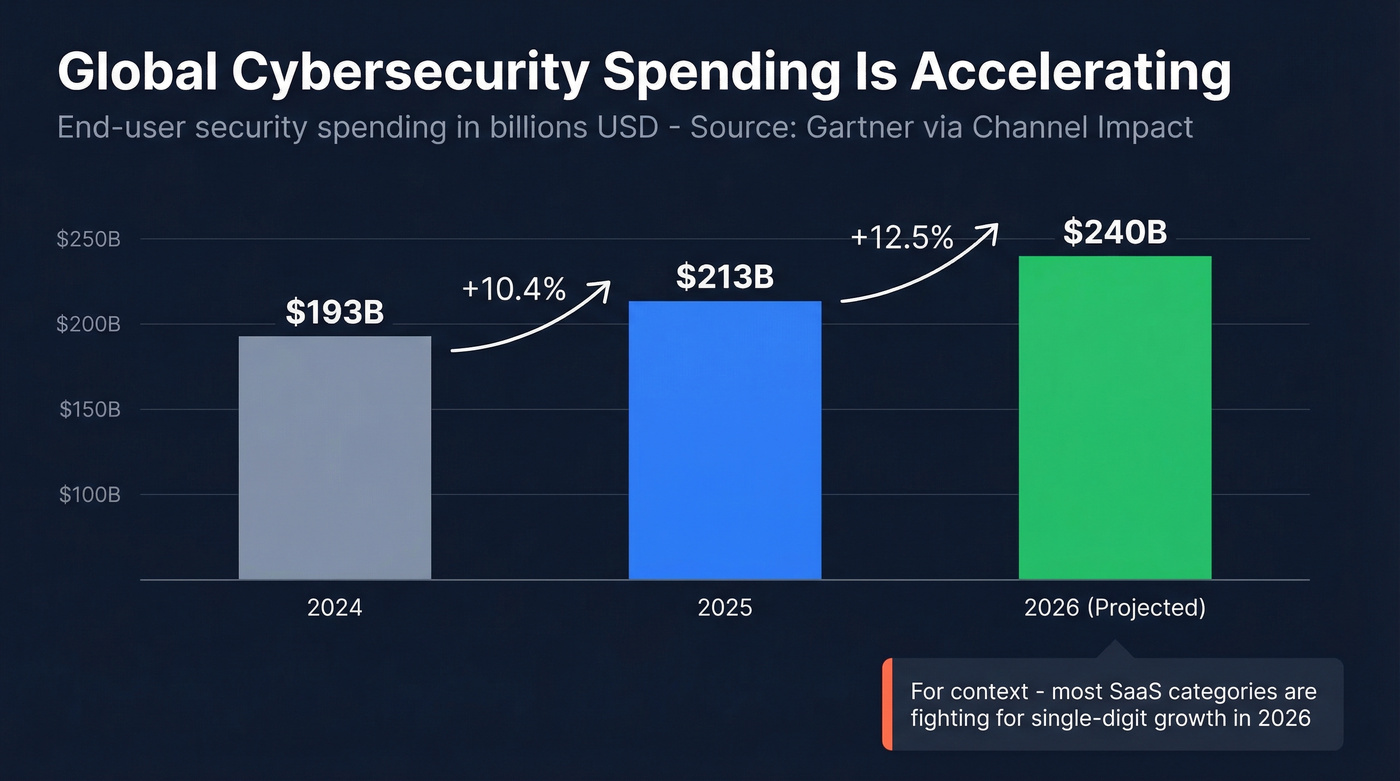
A RevOps lead we know spent six months trying to hire an enterprise AE who understood both SIEM architecture and procurement cycles. She couldn't find one. That's cyber security sales in a nutshell - a vertical where demand for competent sellers far outstrips supply, and the comp reflects it. Global cybersecurity spending hit $213B in 2025 and is projected to reach $240B in 2026, a 12.5% year-over-year jump. The BLS projects 29% job growth for information security analysts through 2034, with roughly 16,000 openings per year.
Every one of those security products needs someone to sell it. Most guides hand you a checklist of certifications and call it a day. Let's get into the money, the buyers, and the actual playbook.
What You Need (Quick Version)
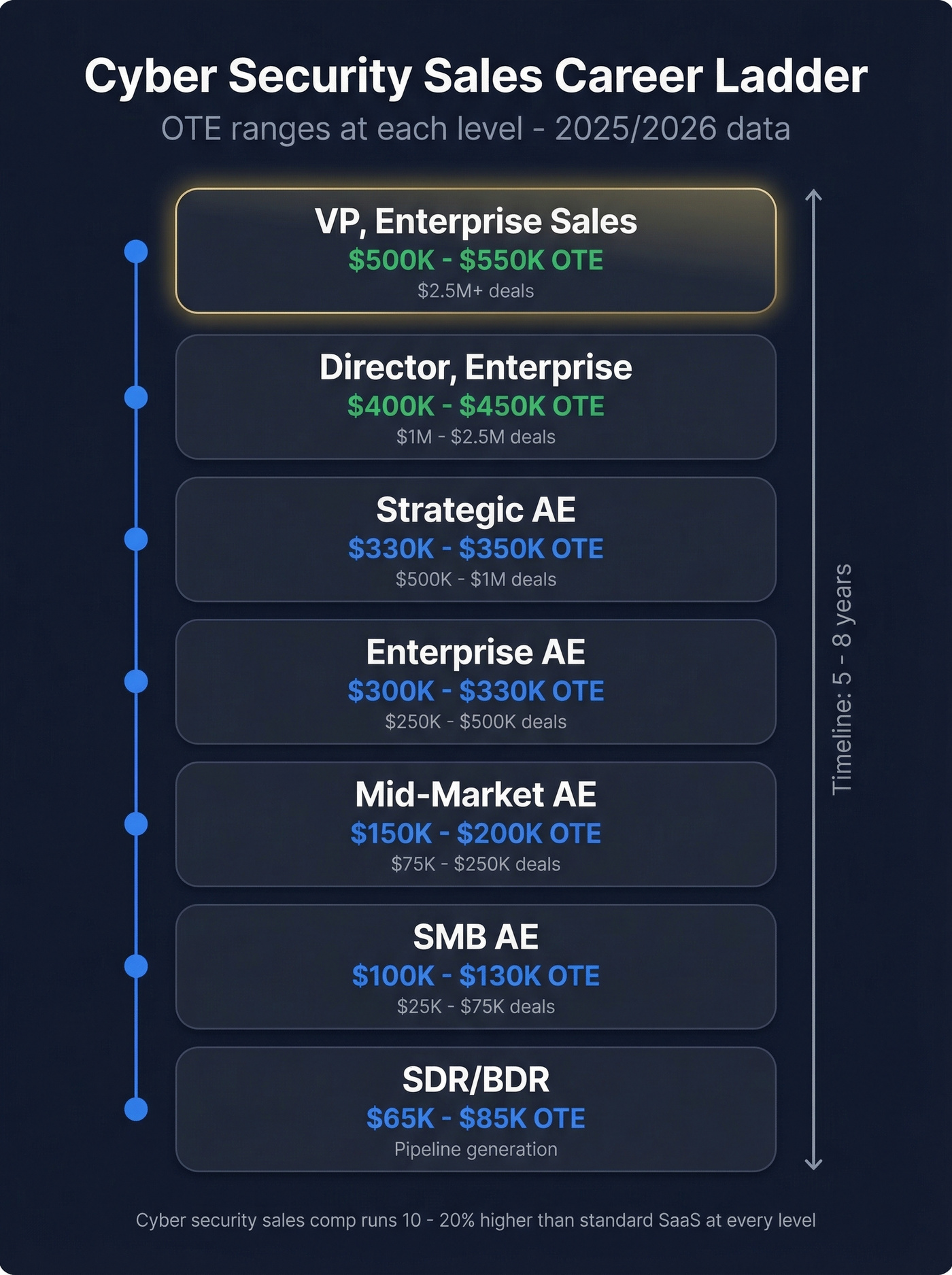
The money is real but wildly variable. An SDR at a cybersecurity startup earns $65K-$85K OTE. A VP of Enterprise Sales at a platform vendor can clear $550K. The gap between those two numbers is navigable in 5-8 years if you pick the right companies and close the right deals.
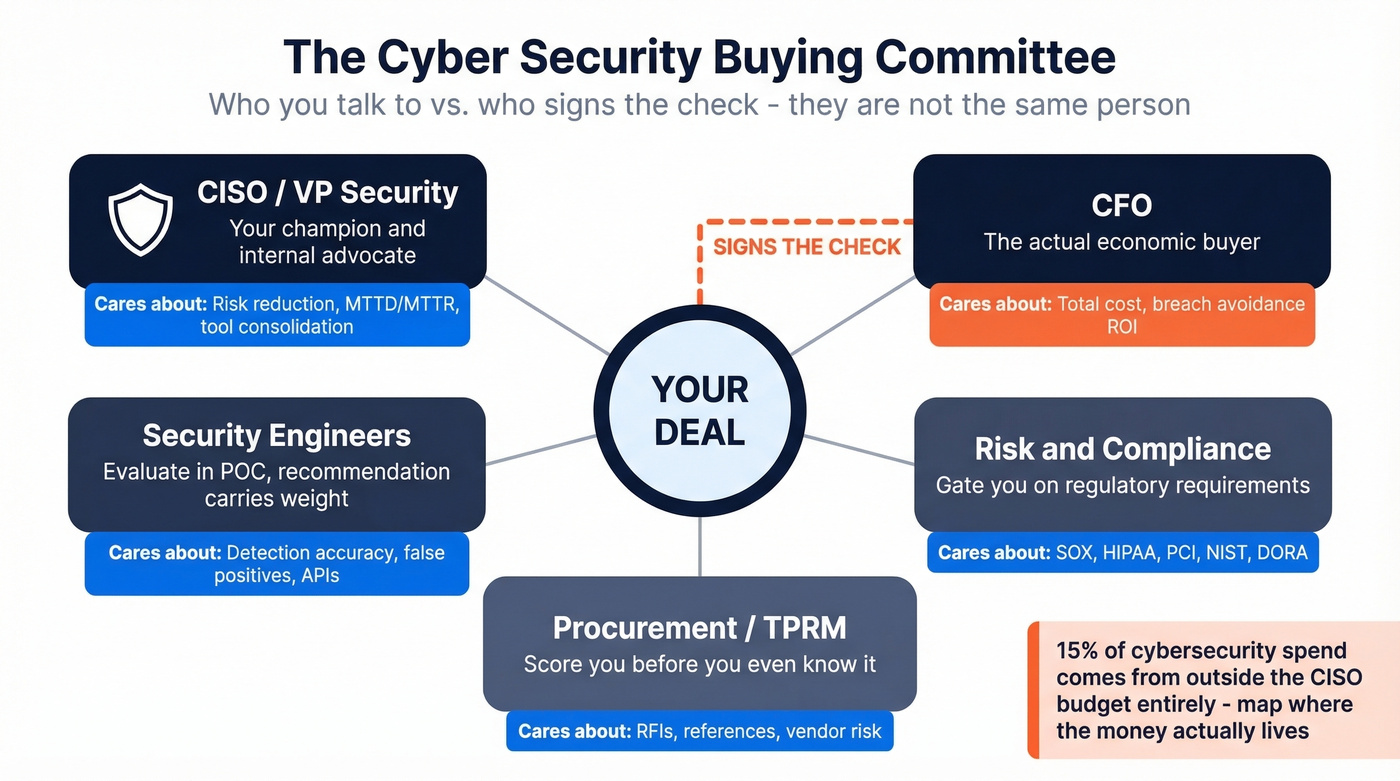
The hardest part isn't learning the tech. It's navigating a buying committee where the budget holder - the CFO - doesn't understand the product, and the technical champion - a security architect - doesn't control the budget. You're translating between two worlds that speak different languages. Get that translation right, build multi-channel credibility, and arm yourself with accurate contact data for buyers who treat unknown emails like phishing attempts, and the rest is execution.
Why This Vertical Wins
Worldwide end-user security spending went from $193B in 2024 to $213B in 2025, with $240B projected for 2026. That's 12.5% growth in a year where most SaaS categories fight for single digits. Security software is the fastest-growing segment within that spend, driven by cloud migration and tools like CSPM and CASB that didn't exist five years ago. Every new attack surface creates a new product category, and every new product category creates sales roles.
The BLS reports a $124,910 median salary for information security analysts - and those are technical roles. Sales roles in cybersecurity routinely exceed $200K+ OTE at mid-market and $300K+ at enterprise. Non-discretionary budgets, complex sales cycles that reward skilled sellers, and a talent shortage that keeps comp elevated make this the single best vertical in tech sales right now.
Here's the nuance, though: while security budgets are growing in absolute terms, their share of total IT spending actually dipped from 11.9% to 10.9% in 2025. Budgets are resilient, but sellers still need to justify every dollar. Boards don't want to be the next breach headline - that fear is your tailwind.
Roles and Compensation
The career ladder follows the standard SaaS progression, but comp runs 10-20% higher at every level because buyer complexity and technical depth demand more from sellers.
| Role | Base | OTE | Typical Deal Size |
|---|---|---|---|
| SDR/BDR | $50K-$65K | $65K-$85K | N/A (pipeline gen) |
| SMB AE | $65K-$80K | $100K-$130K | $25K-$75K |
| Mid-Market AE | $85K-$110K | $150K-$200K | $75K-$250K |
| Enterprise AE | $150K-$165K | $300K-$330K | $250K-$500K |
| Strategic EAE | $165K-$175K | $330K-$350K | $500K-$1M |
| Director, Enterprise | $200K-$225K | $400K-$450K | $1M-$2.5M |
| VP, Enterprise | $250K-$275K | $500K-$550K | $2.5M+ |
| Sales Engineer | $100K-$130K | $140K-$180K | Supports AE deals |
SDR through Mid-Market AE ranges are industry estimates for cybersecurity vendors; enterprise tiers are sourced from Betts Recruiting's 2025 compensation data. SE pay is anchored to BLS data ($116,950 median for May 2023) and ZipRecruiter ($122,890 average), with OTE reflecting typical variable comp structures.
Enterprise AE quotas scale by company funding stage - roughly $900K at Seed/Series A up to $1.35M at Series D. That's a 50% increase in target as the company matures. Technical sectors like AI, cloud security, and infrastructure command premium comp versus more commoditized SaaS categories.
Real talk: a $350K OTE means nothing if only 48% of reps hit quota. The ceiling is high. The floor is your base salary. (If you want to benchmark OTE math across roles, see our guide to OTE.)
How to Break In
You don't need a CISSP or a background in penetration testing. Most successful reps come from other SaaS verticals - martech, HR tech, DevOps tools - and learn the security domain on the job.
Pick your employer type wisely. High-growth startups like Wiz and Abnormal Security let you wear multiple hats and learn fast. MSSPs and VARs like GuidePoint Security expose you to multiple vendor portfolios. Established platforms like CrowdStrike, Palo Alto Networks, and Zscaler offer world-class enablement but aggressive quotas.
Get one certification - then stop. CompTIA Security+ gives you enough technical credibility for intelligent conversations with security engineers. Google's free Foundations of Cybersecurity course on Coursera is a solid starting point. But a sales methodology cert in MEDDIC or MEDDPICC matters more than any technical cert for your actual quota (start with MEDDIC sales qualification and how to handle the MEDDPICC economic buyer).
Study your buyer, not the textbook. This is the contrarian take that experienced cyber sellers agree on. The consensus on r/sales is clear: you don't need to become a security expert. You need to become an expert on your product, your buyer's problems, and the three to four use cases where your solution wins. Your SE handles the deep technical questions. You handle the business case, the stakeholder navigation, and the close.
The fastest path from zero to carrying a bag is SDR at a mid-stage cybersecurity vendor. Twelve to eighteen months of pipeline generation, then promote to AE. If you're ramping fast, a simple 30-60-90 day plan helps you avoid random activity.

Cyber security buyers are professionally paranoid - they won't open an email from an unknown sender hitting an unverified address. Prospeo gives you 98% accurate emails and 125M+ verified mobile numbers so you actually reach the CISO, not their spam folder. At $0.01 per email, even an SDR's budget covers it.
Stop getting flagged. Start getting meetings with security decision-makers.
How to Actually Sell Cybersecurity
Selling security is different from selling most SaaS. Your buyers are professionally paranoid, technically sophisticated, and drowning in vendor pitches. A practitioner on r/sales who progressed from SDR to Enterprise AE across Oracle, CrowdStrike, Zscaler, and SOCRadar laid out the rules that experienced sellers live by.
The Buying Committee
The single biggest mistake new sellers make is treating the CISO as the economic buyer. The CISO is your champion, your technical validator, and your internal advocate. The CFO signs the check. Understanding this distinction changes your entire deal strategy. (If you want a framework for this, see technical buyer vs economic buyer.)
| Stakeholder | What They Care About | Your Approach |
|---|---|---|
| CISO / VP Security | Risk reduction, tool consolidation, MTTD/MTTR | Quantify risk in dollars |
| Security Engineers | Detection accuracy, false positives, APIs, deployment complexity | Demo-first; let your SE lead |
| Risk & Compliance | SOX, HIPAA, PCI, NIST, DORA | Compliance docs upfront |
| Procurement / TPRM | RFIs, scoring, references | Prepare before they ask |
| CFO | Total cost, breach avoidance | Risk-adjusted ROI |
About 15% of corporate cybersecurity spend comes from outside the CISO's budget entirely. Map where the money actually lives - sometimes it's IT infrastructure, sometimes risk management, sometimes a board-mandated line item. Bring legal, procurement, and finance into the conversation earlier than feels comfortable.
When to Strike
Not every quarter is equal. The best sellers time outreach around moments when budgets loosen and urgency spikes: breach incidents at the prospect's company or a high-profile competitor, regulatory deadlines like DORA enforcement or PCI DSS 4.0 compliance windows, a new CISO's first 90 days when they audit the stack, Q3/Q4 budget planning cycles (start conversations in Q2), and board-level attention after a competitor breach or regulatory fine.
Handling Objections
Three objections come up in nearly every deal.

"We already have a solution." Don't attack the incumbent - ask what gaps they're patching manually. Every security team has workarounds they hate.
"We're locked into a contract." Offer a parallel POC that proves value before their renewal date. Plant the seed 6 months early.
"Show me the ROI." Translate your product's impact into breach cost avoidance using their industry's average incident cost. A $4.88M average breach cost makes a $200K platform look cheap.
Outreach That Works
Generic cold outreach to CISOs is dead. They assume you're a phishing attempt - and honestly, can you blame them?
Don't start at the top. Engage security engineers and architects first. They evaluate your product in a POC, typically 2-4 weeks, and their recommendation carries enormous weight with the CISO. Be specific about the one problem you solve. "We help mid-market companies reduce MTTR by 40% for cloud workload threats" lands. "We're an AI-powered cybersecurity platform" gets ignored.
Use multi-channel outreach - what one practitioner calls the "MFA approach" to sales. Email, phone, relevant community engagement, and warm introductions through your SE network. A bounced email to a CISO's old address wastes more than a touchpoint; it burns credibility. Prospeo's real-time verification and 7-day data refresh cycle means your first touch actually lands, which matters in a vertical where buyers are trained to distrust unknown senders. For more on what actually works now, borrow a few sales prospecting techniques and tighten your sales communication.
Lead with tangible evidence, not your Magic Quadrant position. Threat intelligence reports, breach cost data, customer case studies with specific metrics - these open doors. Buzzwords close them.
Product Categories Worth Selling
Some categories pay better and grow faster than others. Here's where the growth and comp upside concentrate.
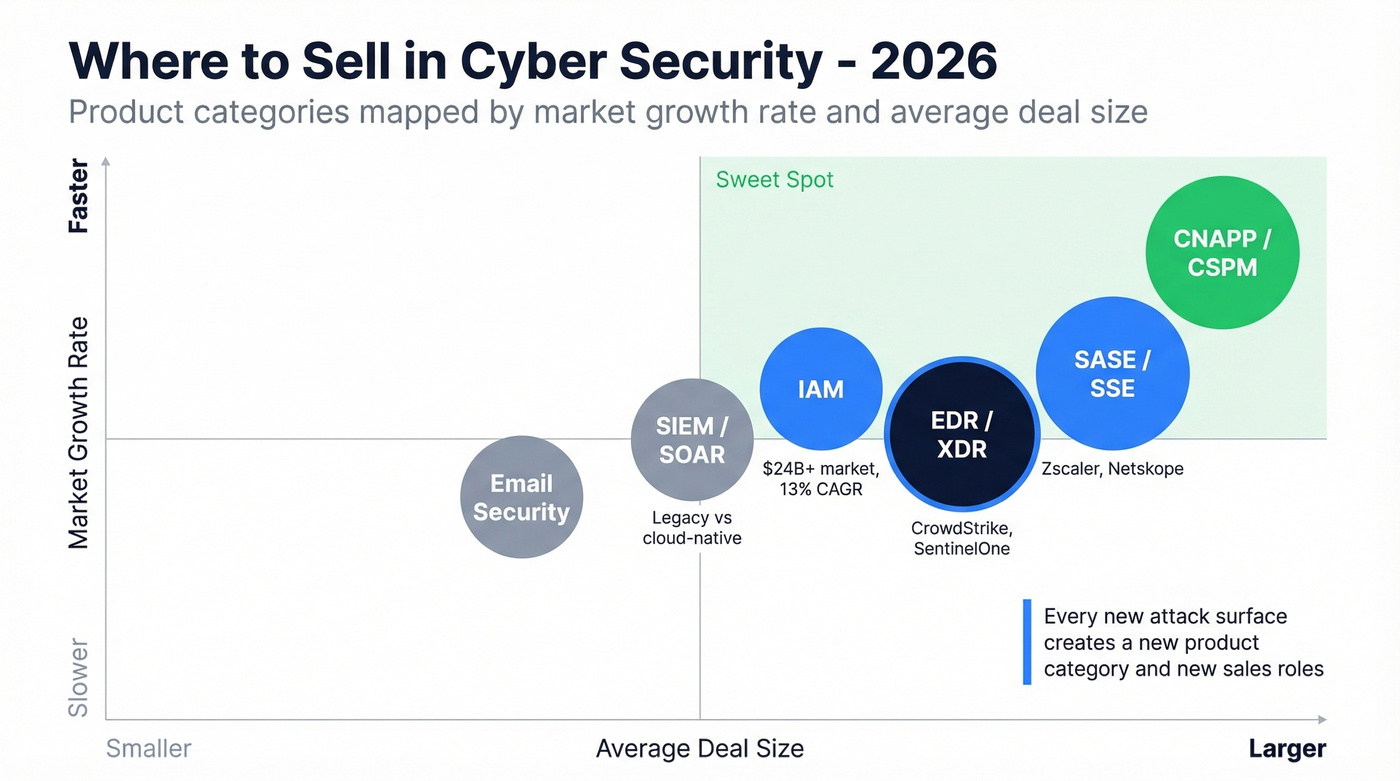
EDR/XDR and SIEM/SOAR form the detection and response backbone. CrowdStrike and SentinelOne dominate EDR, while legacy SIEM players like Splunk (now Cisco) compete with cloud-native upstarts. These are mature categories with large deal sizes and well-established sales motions.
IAM is a $24B+ market growing at ~13% annually, driven by zero trust adoption. Okta, CyberArk, and SailPoint are the big names.
SASE/SSE - led by Zscaler and Netskope - offers high deal sizes and complex sales cycles that reward experienced sellers. CNAPP/CSPM is the breakout category. Wiz is the poster child. If you can get in early at a CNAPP vendor, the equity upside is real.
Email security from Abnormal Security, Proofpoint, and Mimecast sells into every company with an inbox. GRC from Drata, Vanta, and ServiceNow is growing fast as regulatory pressure mounts. MDR from Arctic Wolf and Expel is particularly strong for selling into mid-market companies without large security teams.
Skip commoditized endpoint antivirus - margins are thin, differentiation is weak, and the sales motion is a race to the bottom on price.
One thing we've noticed in 2026: AI-native security products are reshaping buyer expectations. Prospects now expect autonomous detection and response capabilities in demos, and POC conversations increasingly center on how AI reduces analyst workload rather than just improving detection rates. If you're choosing a category, pick one where AI is a genuine differentiator - not just a marketing label slapped on a rules engine.
Where to Work
RepVue's rankings give you employee-reported data on what it's actually like to sell at these companies:
| Company | RepVue Score | % Hitting Quota | Notes |
|---|---|---|---|
| Saepio | 91.16 | 78% | Strong culture + comp |
| GuidePoint Security | 87.09 | 70% | High PMF; MSSP/VAR model |
| Palo Alto Networks | 85.84 | 48% | Strong PMF; aggressive targets |
| CrowdStrike | 82+ | ~55% | Best-in-class enablement |
| Zscaler | 80+ | ~50% | SASE leader; high deal sizes |
The full RepVue Top 20 includes Fortinet, SentinelOne, Abnormal Security, and others - worth browsing if you're actively interviewing.
A high-scoring company where only 48% hit quota tells you the product-market fit is strong but the targets are aggressive. Palo Alto Networks is a great place to learn enterprise security selling - just know that the quota will stretch you.
For maximum learning, target high-growth startups like Wiz, Abnormal Security, or Island. For stability and enablement, established platforms like CrowdStrike, Zscaler, and Fortinet offer structured career paths and brand recognition. For breadth of exposure, MSSPs and VARs like GuidePoint give you experience across multiple vendor portfolios - invaluable if you want to eventually move vendor-side.
We've seen reps who started at an MSSP and then moved to a vendor command higher comp because they understood channel dynamics that most direct sellers never learn.
Your Prospecting Tech Stack
Most tools will be chosen by your employer. But understanding the stack - and knowing where to invest your own time - gives you an edge.
| Category | Tool | Typical Cost | Who Pays |
|---|---|---|---|
| CRM | Salesforce, HubSpot | $25-$300/user/mo | Employer |
| Sales Engagement | Outreach, Salesloft | ~$100-$150/user/mo | Employer |
| Conversation Intel | Gong | ~$100-$150/user/mo | Employer |
| Prospecting & Data | Prospeo | Free tier; ~$0.01/email | You or employer |
| Prospecting & Data | ZoomInfo | $15K-$40K/yr | Employer (enterprise) |
Your engagement layer and conversation intelligence will be provided by your employer. Where you differentiate yourself is in the data layer - having better, fresher contact information than your peers means more conversations, more pipeline, and more closed deals. Prospeo gives you 300M+ professional profiles, 143M+ verified emails at 98% accuracy, and 125M+ verified mobile numbers with a 30% pickup rate. Data refreshes on a 7-day cycle versus the 6-week industry average, and intent data tracks 15,000 topics to surface companies actively evaluating security solutions. (If you're comparing providers, our breakdown of data enrichment services and B2B company data can help.)

Navigating a 6-person buying committee means you need direct contact data for the CISO, the CFO, and every stakeholder in between. Prospeo's 300M+ profiles with 30+ filters - including technographics and buyer intent across 15,000 topics - let you map the entire security buying committee in minutes, not weeks.
Map the full buying committee before your competitor finds the CISO.
FAQ
Do I need a technical background?
No. Most successful cybersecurity sellers come from other SaaS verticals. You need to understand your product and your buyer's problems, not become a security engineer. CompTIA Security+ helps with credibility but isn't required.
How long are enterprise sales cycles?
SMB deals close in 2-6 weeks. Mid-market runs 2-4 months. Enterprise takes 4-9 months, including a 2-4 week POC, procurement review, and legal sign-off.
What's realistic first-year SDR OTE?
$65K-$85K OTE with base around $50K-$65K. Top performers at well-funded startups exceed $90K. The real payoff comes after promotion to AE within 12-18 months.
What prospecting tools do cybersecurity reps use?
Most teams run Salesforce or HubSpot, a sales engagement platform like Outreach, and a data provider for verified contacts. Prospeo is popular with individual reps for its 98% email accuracy and free tier of 75 credits per month - critical when reaching security buyers who ignore unverified outreach.
Is this vertical better than general SaaS?
For most reps, yes. The market grows at 12.5% annually, budgets survive downturns because security is non-discretionary, and enterprise comp ceilings are among the highest in tech sales. The tradeoff is longer cycles and more technical complexity.